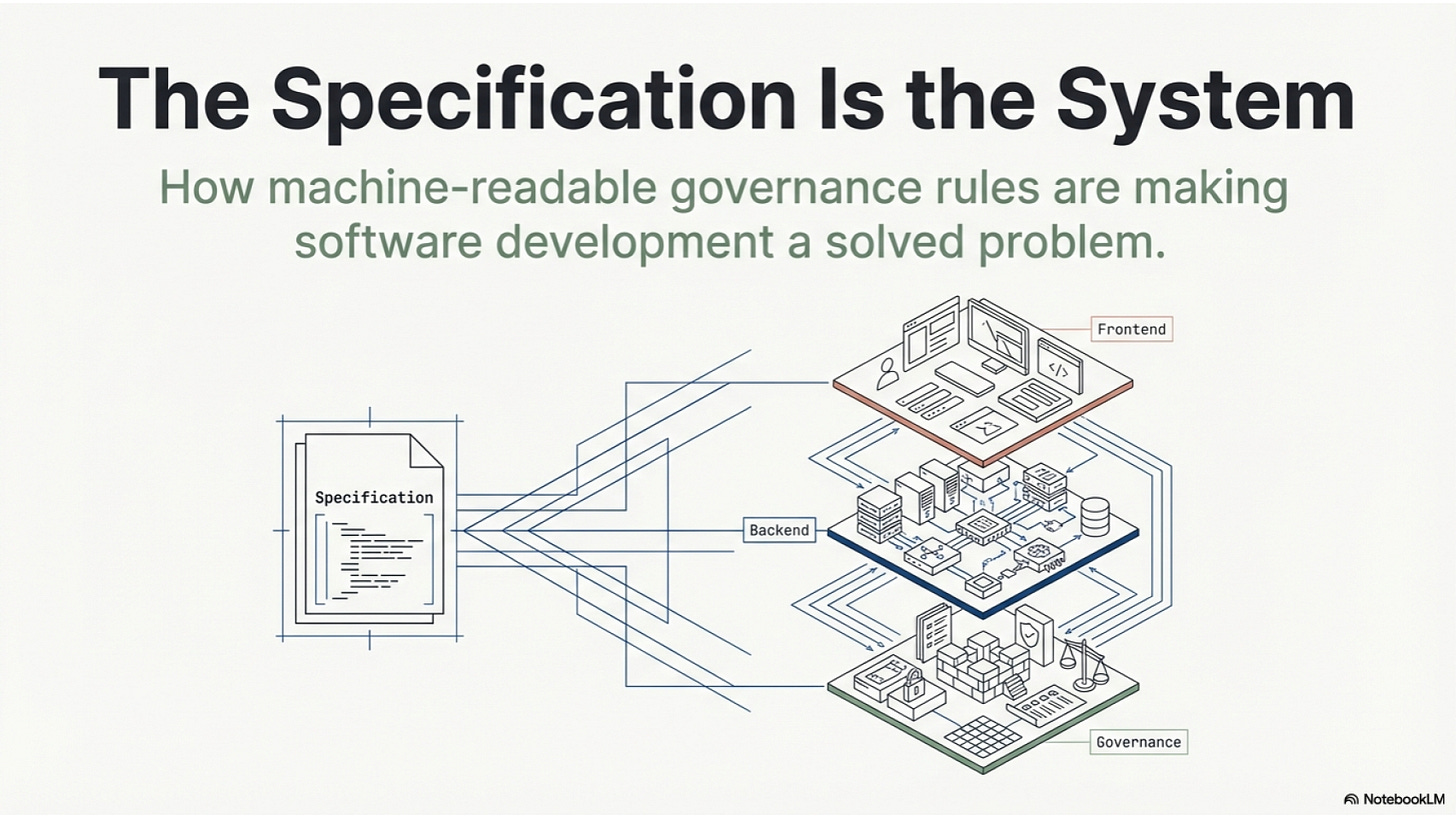
The Specification Is the System
How machine-readable governance rules are about to make software development a solved problem — and what comes after
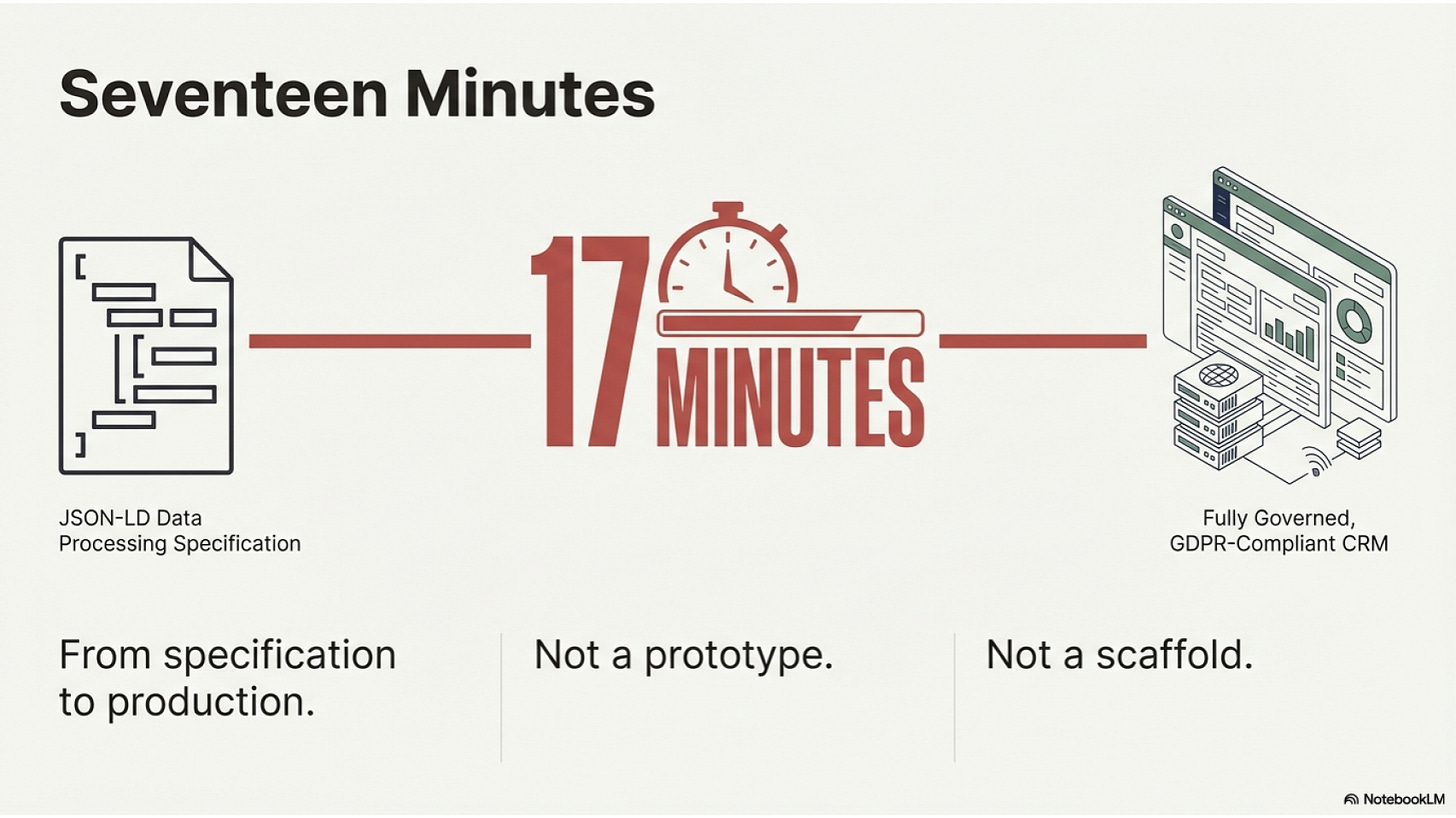
Seventeen minutes.
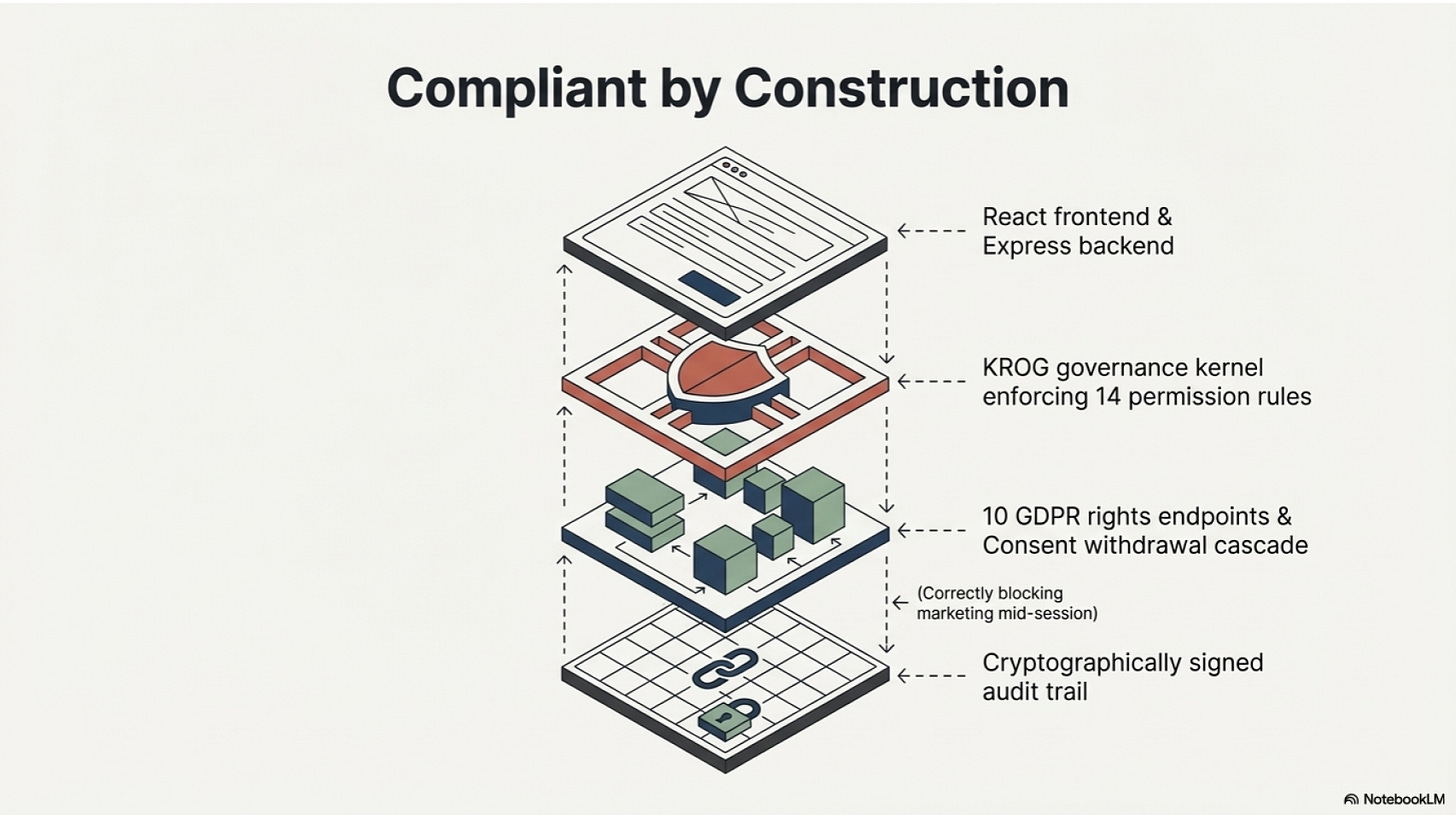
That is how long it took to generate a fully governed, GDPR-compliant CRM system from a JSON-LD data processing specification. Not a prototype. Not a scaffold. A running system, a KROG governance kernel enforcing permission rules, a cryptographically signed audit trail, 10 GDPR rights endpoints, and a consent withdrawal cascade that correctly blocked marketing and profiling operations mid-session.
Seventeen minutes. From specification to production.
This is not a story about how fast Claude Code runs. It is a story about what it means when the specification is the system — and what that implies for every domain where decisions have to be made, rules have to be enforced, and machines have to act.
What We Built and How
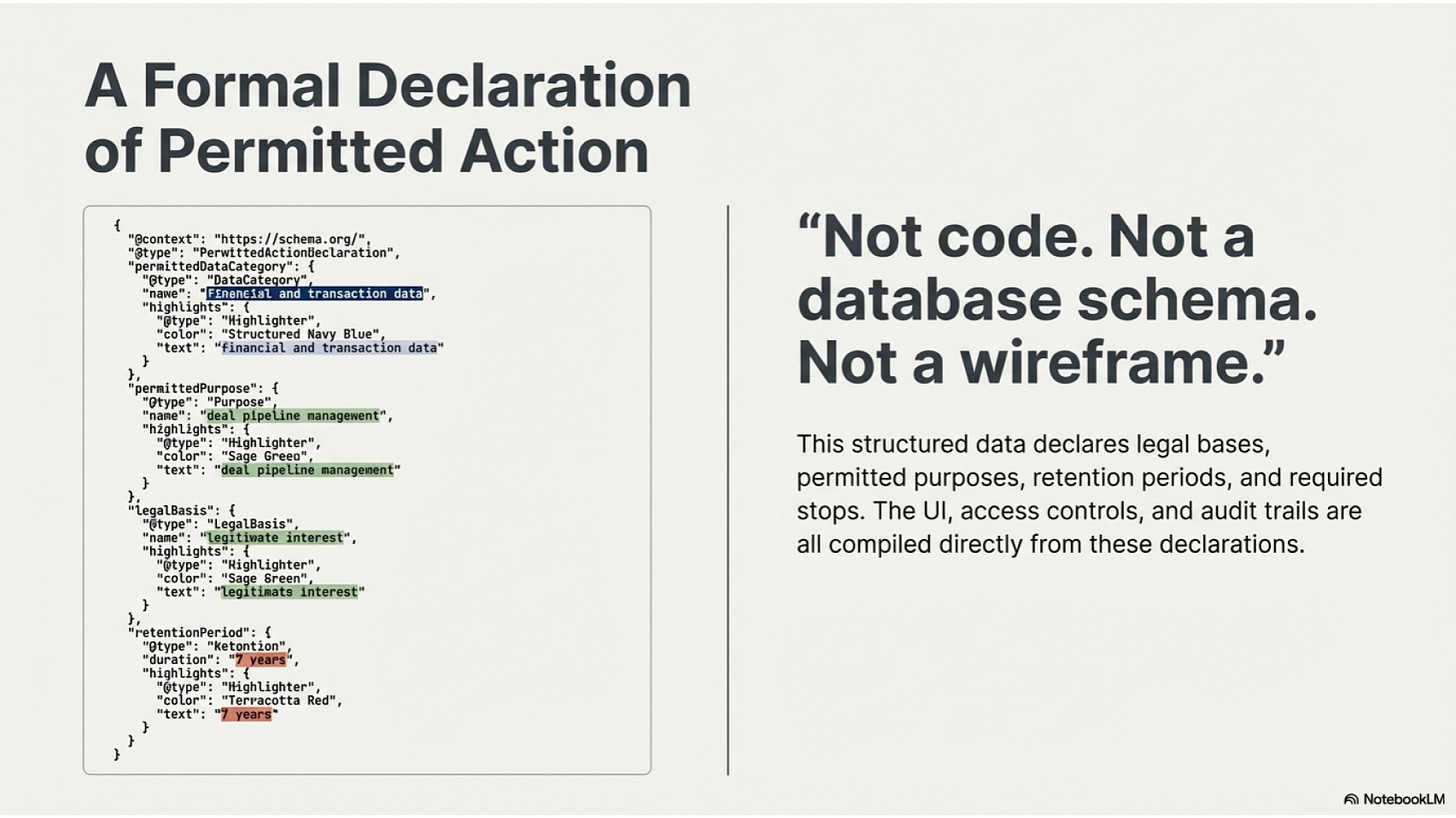
The starting point was a JSON-LD document. Roughly 400 lines of structured data describing a single thing: what a company is permitted to do with personal data it holds about its customers.
Not code. Not a database schema. Not a wireframe. A formal description of data processing operations — each operation declaring its legal basis, its permitted purpose, its data categories, its retention period, its permitted recipients, and the conditions under which it must stop.
The formal specification, when presented in natural language, says: we process financial and transaction data for deal pipeline management, under legitimate interest, retained for 7 years because the law requires it.
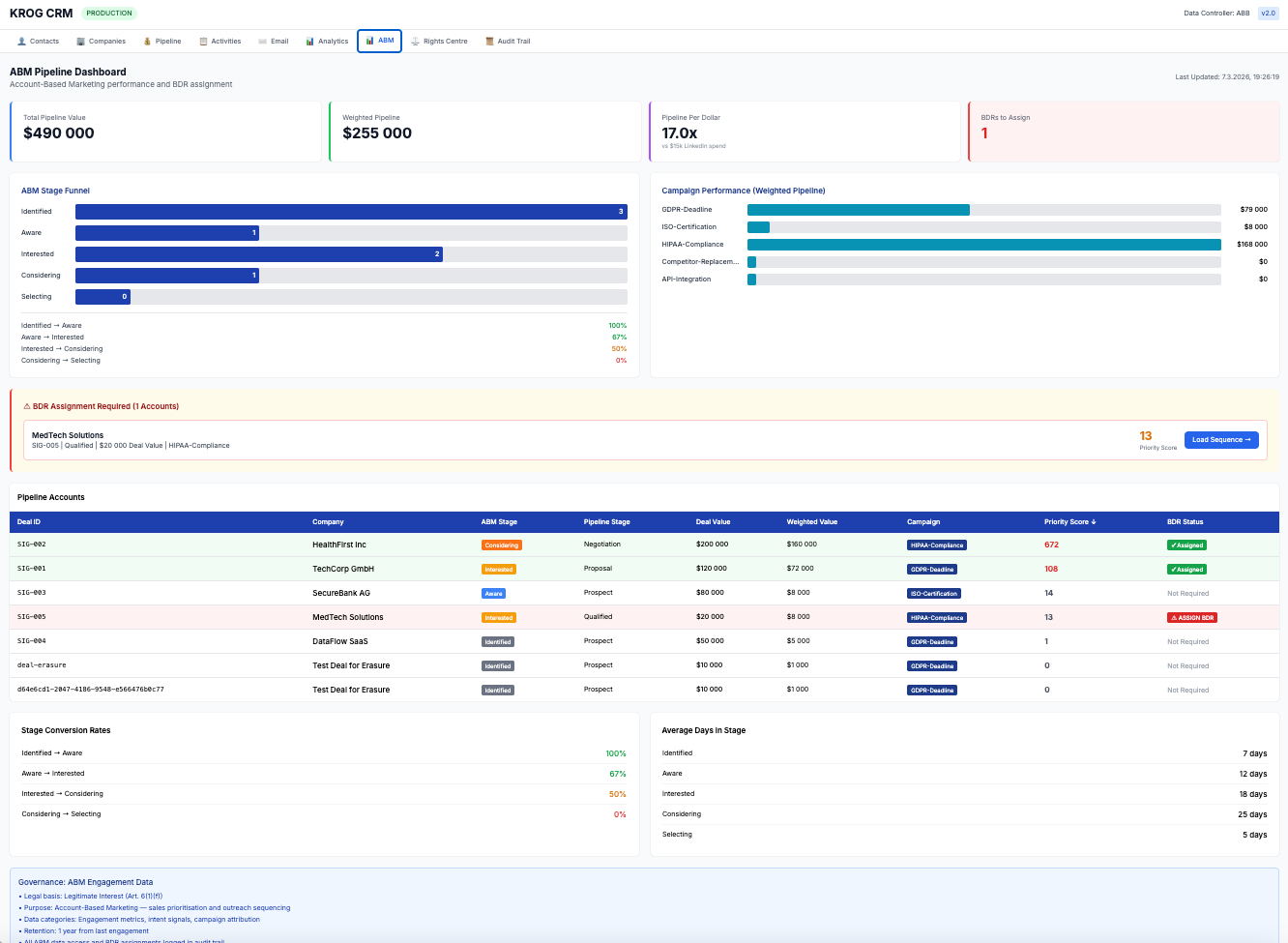
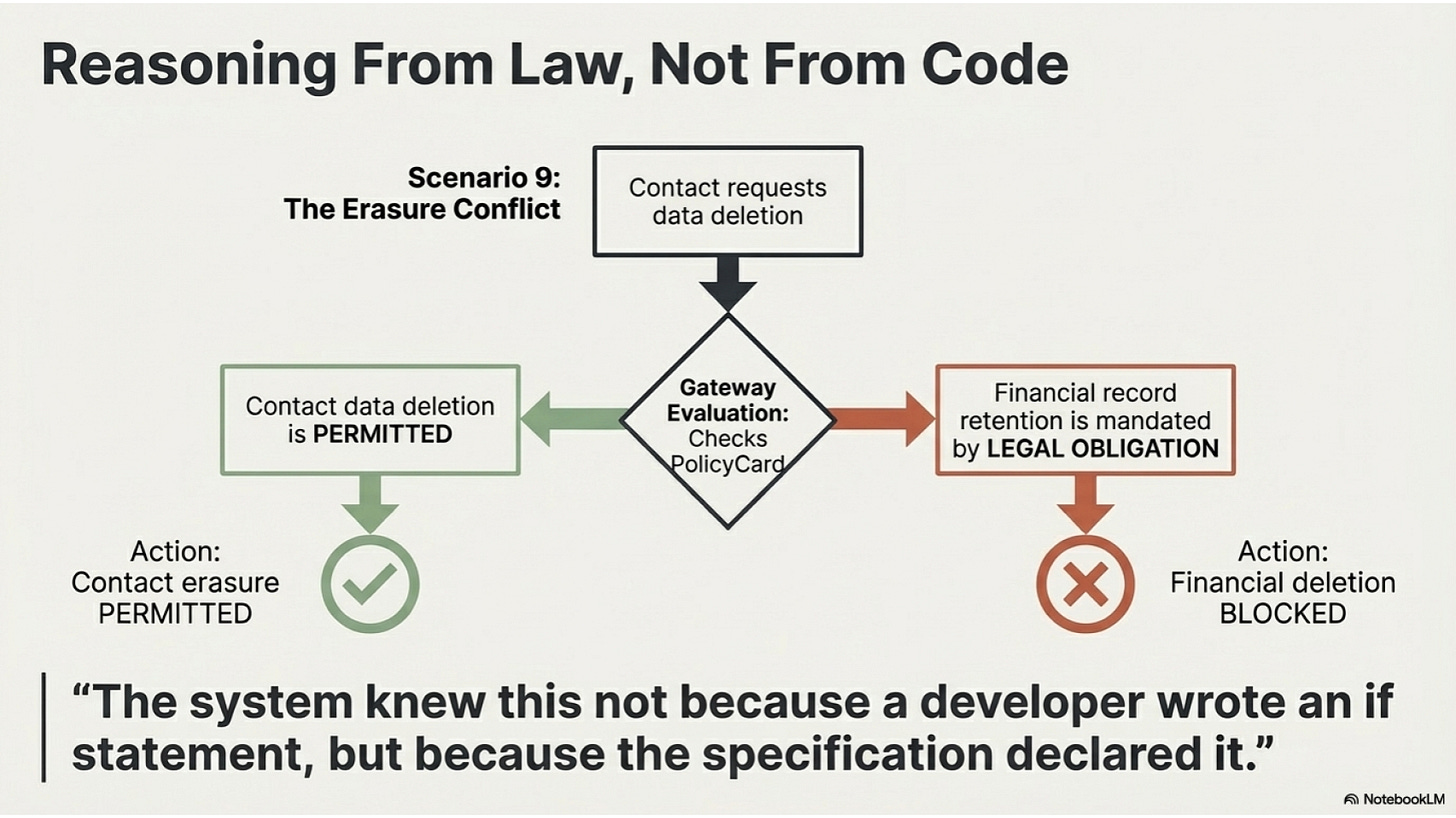
From this specification — from this formal declaration of what is permitted and what is forbidden — a complete CRM system was generated. The UI was rendered from the data categories. The access controls were compiled from the legal bases. The audit trail was structured around the processing operations. The rights endpoints (erasure, portability, rectification, objection) were generated with the retention rules already baked in: financial records cannot be erased on request because legal obligation overrides data subject rights.
The system knew this not because a developer wrote an if statement, but because the specification declared it.
The KROG Layer: Rules That Govern the Generator
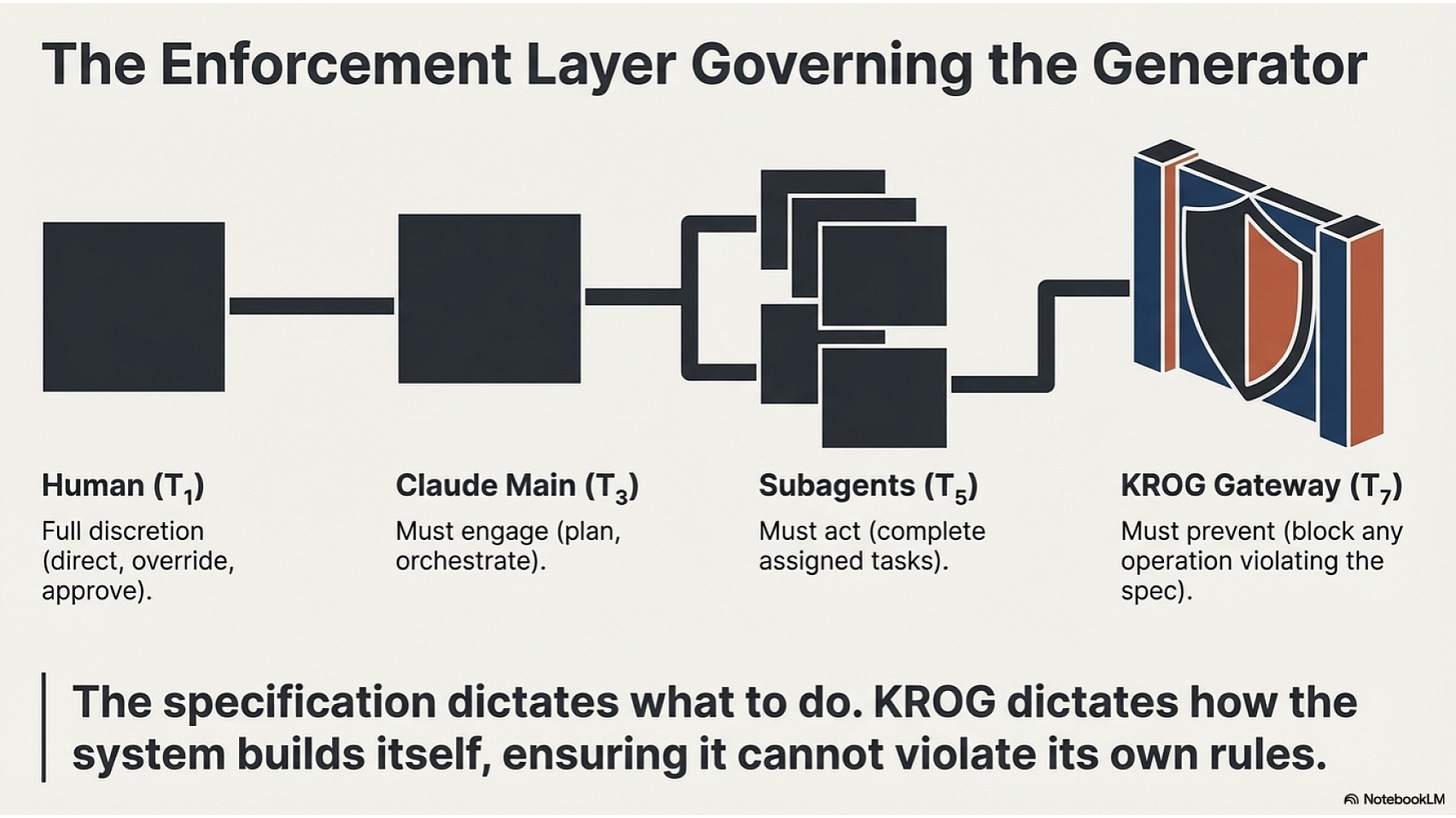
The specification tells the system what to do. The KROG rules tell the system how to build itself.
KROG is a deontic rule engine derived from legal position theory — the same formal structure that governs how rights and obligations relate to each other in law. Every agent in the build process has a state type (what it can, must, or cannot do) and every pair of agents has a relationship type (their bilateral obligation relationship).
When the CRM prompt was written, it was written as a KROG topology.
The Gateway is the enforcement layer that makes this different from ordinary code generation. Before any data operation executes in the generated CRM — before a contact record is read, before a deal value is written, before a consent record is checked — the Gateway evaluates the operation against the PolicyCard compiled from the specification.
PERMIT: the operation proceeds and is logged. BLOCK: the operation is refused, the reason is recorded, the audit trail is updated.
This is not soft guidance. It is a formal constraint. The system cannot violate its own specification.
The prompt for the CRM generation included this verification gate: all 14 governance scenarios must pass before any output is presented. Scenario 9 — partial erasure, where a contact requests deletion but financial records must be retained — passed because the specification declared legal obligation as a competing basis, and the governance kernel correctly blocked the financial deletion while permitting the contact erasure.
The system reasoned from law, not from code.
Two Interfaces, One Specification
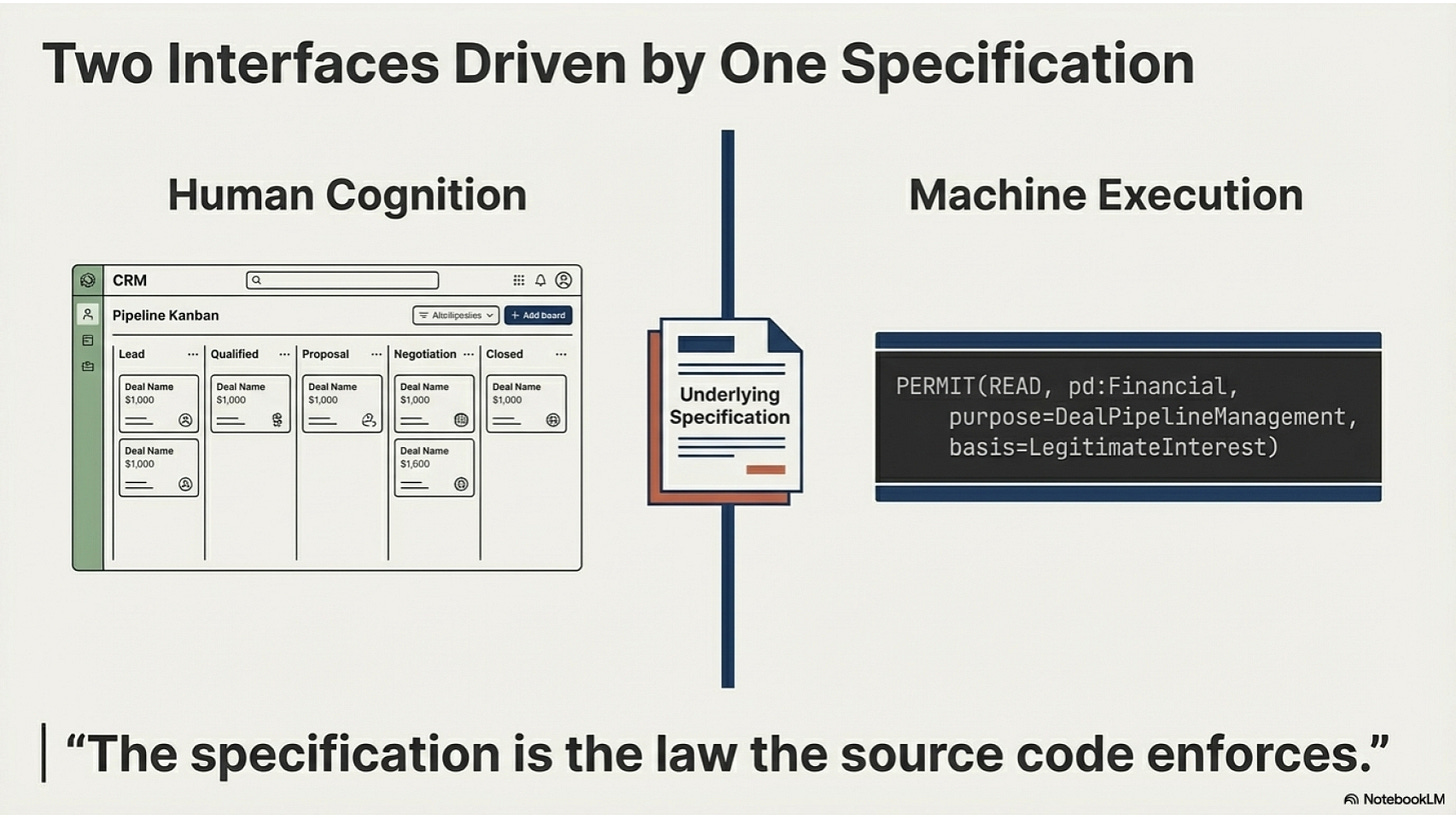
Here is the architectural insight that matters.
The CRM has a UI. It has navigation tabs, deal cards, pipeline views, a dashboard. Humans use these. The UI is rendered from the data categories declared in the specification — contact data generates a Contacts tab, deal pipeline data generates a Pipeline tab, financial records are visible in the Analytics view.
But the CRM also has a machine interface. The same specification that generated the UI also generates the governance rules for every AI agent, automated process, or external system that touches the data.
A human looks at the Pipeline tab and sees a Kanban board. An AI agent looks at the specification and sees: PERMIT(READ, pd:Financial, purpose=DealPipelineManagement, basis=LegitimateInterest).
Same data. Same rules. Two interfaces — one designed for human cognition, one designed for machine execution.
This is the architectural shift. We have spent thirty years building software that humans operate through interfaces designed for human cognition. The next thirty years will be spent building systems that both humans and machines can operate — each through the interface appropriate to their mode of cognition — governed by the same underlying specification.
The specification is not the source code. The specification is the law the source code enforces.
What This Unlocks: Every Domain Where Rules Govern Action
Software was the first domain because software is the most legible. A JSON-LD specification generates a CRM. The same mechanism — formal specification of permitted operations → automated generation of systems that enforce those permissions — applies to every domain where:
Rules govern what actors can do
Multiple actors (human and machine) must operate under the same rules
Violations must be detected, logged, and prevented
That is not a narrow domain. That is most of human activity.
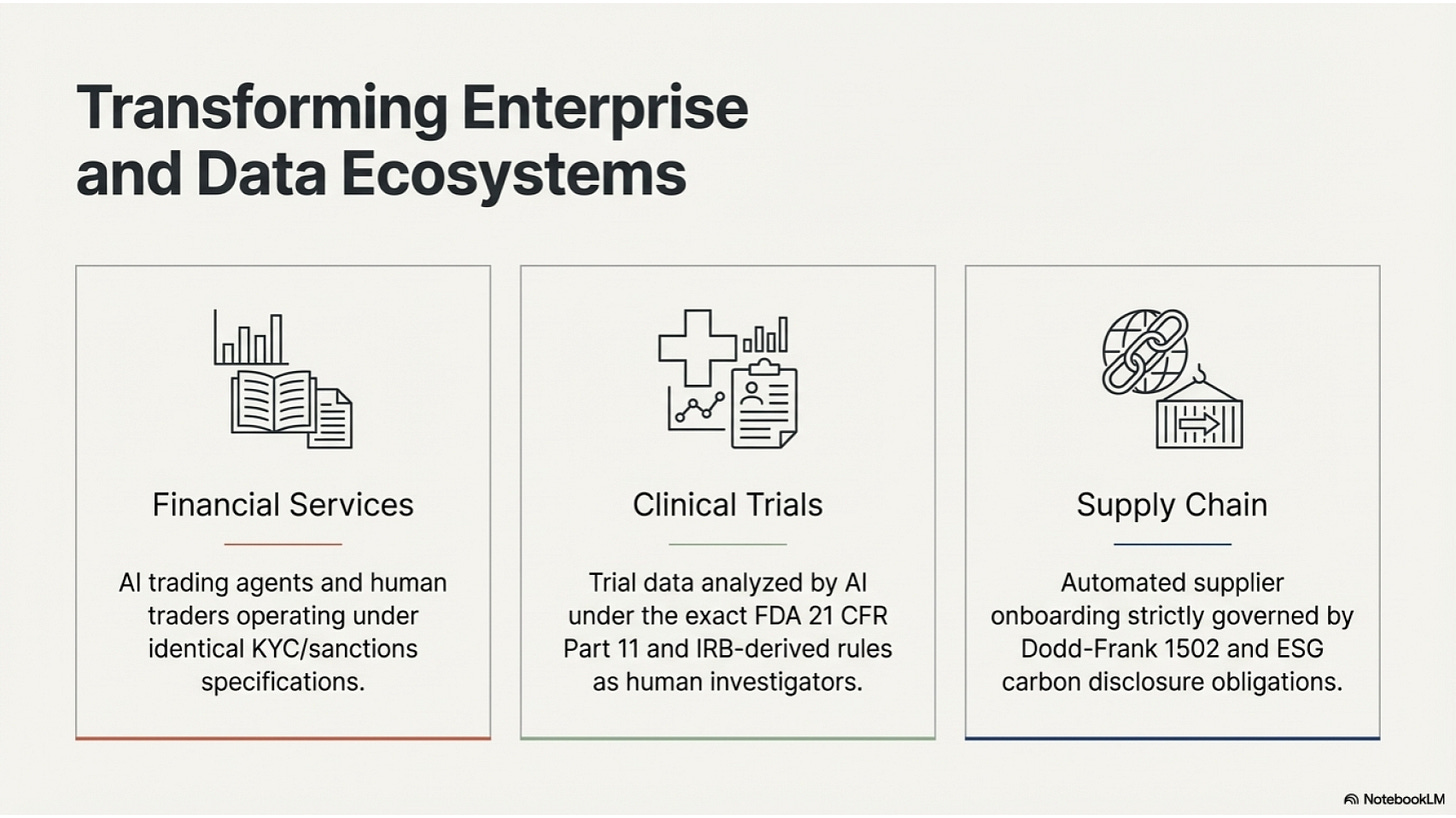
Financial services. A payment processing specification declares: permitted currencies, permitted counterparties, transaction limits by jurisdiction, KYC requirements before execution, sanctions screening obligations. From this, generate the payment gateway, the compliance dashboard, the transaction monitor, the regulatory reporting pipeline. Any AI agent executing a trade operates under the same specification as the human trader reviewing the blotter. Same rules. Different interfaces.
Clinical trials. A data governance specification declares: permitted data collection per protocol, consent requirements per jurisdiction, data sharing agreements with CROs, retention obligations under FDA 21 CFR Part 11. Generate the trial management system, the adverse event reporter, the audit-ready data package. An AI agent analysing trial data operates under the same IRB-derived rules as the clinical investigator reviewing the protocol. The specification is the IRB approval made executable.
Supply chain. A procurement specification declares: permitted suppliers by tier, conflict minerals prohibitions under Dodd-Frank Section 1502, modern slavery due diligence requirements, carbon disclosure obligations. Generate the supplier onboarding portal, the compliance questionnaire, the audit workflow, the ESG reporting dashboard. An AI agent qualifying a new supplier against the specification cannot approve a supplier that violates the rules — not because a developer wrote the check, but because the prohibition is in the specification.
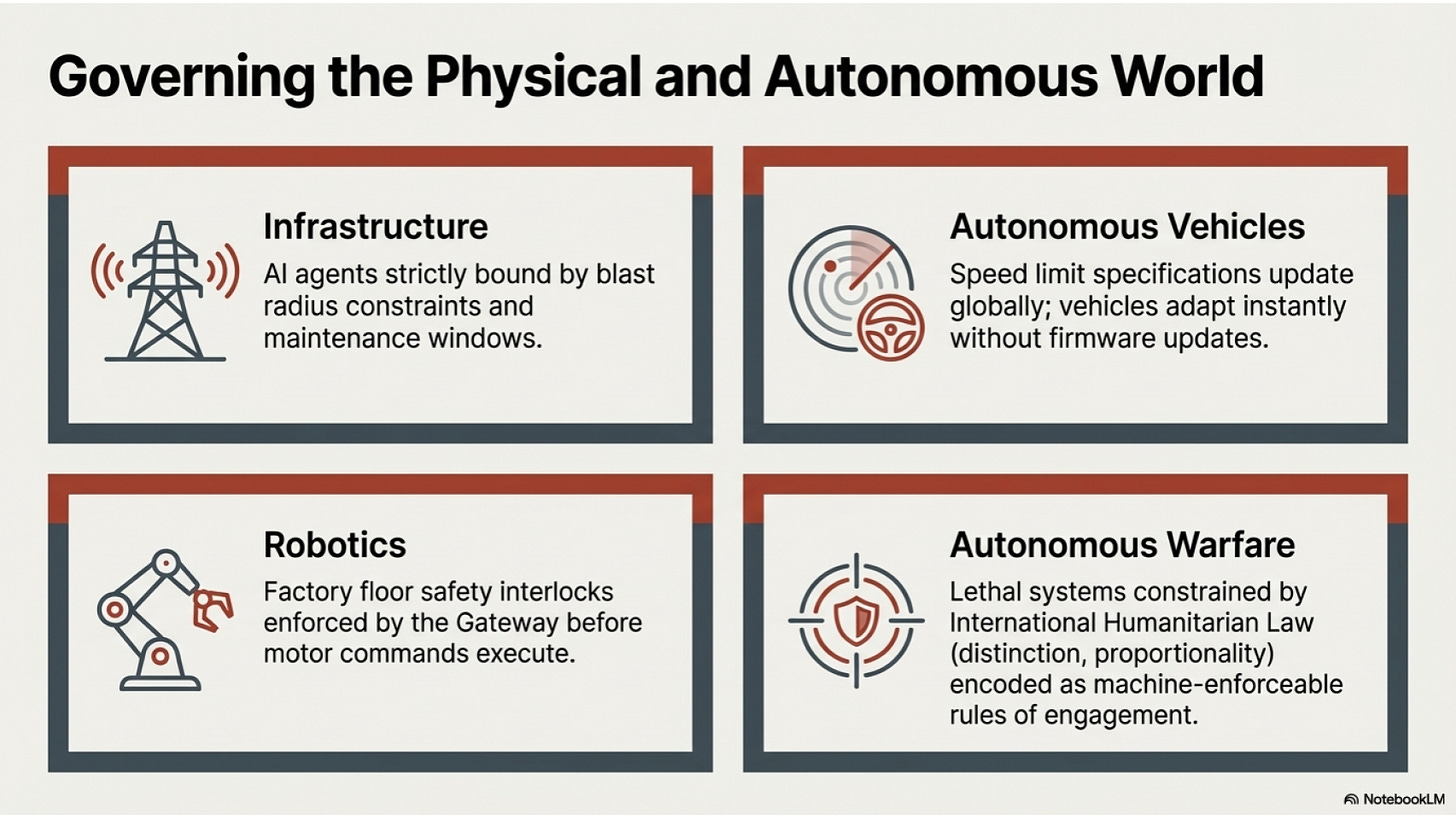
Infrastructure operations. A data centre specification declares: permitted maintenance windows, change approval requirements, blast radius constraints, rollback obligations. Generate the change management workflow, the automated deployment gates, the incident response runbook. An AI agent executing infrastructure changes cannot deploy outside a maintenance window — the specification governs the agent.
Autonomous vehicles. A traffic operations specification declares: permitted speeds by zone, right-of-way rules at intersections, emergency vehicle preemption protocols, liability assignment by scenario. The vehicle’s decision system operates against this specification in real time. When a human regulatory body updates the speed limit in a school zone, the specification updates, and every vehicle operating under it adjusts — without a firmware update, without a developer writing new if statements.
Robotics and industrial automation. A factory floor specification declares: permitted operating zones per robot, human proximity protocols, tool change authorities, safety interlock requirements. Generate the robot task scheduler, the safety monitoring system, the incident log. A robot operating autonomously on the factory floor cannot enter a human safety zone — the specification forbids it, and the KROG Gateway enforces it before the motor command executes.
Autonomous warfare. This is where the stakes become explicit. A rules of engagement specification declares: permitted target categories under international humanitarian law, distinction obligations (civilian vs combatant), proportionality constraints (collateral damage thresholds), precaution requirements (confirmation before engagement), and chain of command authorisation requirements. An autonomous weapons system operating against this specification cannot engage a target that fails the distinction test — not because a software engineer anticipated every scenario, but because the IHL rules are formally encoded in the specification and the governance kernel enforces them before any action executes. The specification is the rules of engagement, made machine-enforceable. The audit trail is the after-action report, generated automatically. Whether this architecture is sufficient to govern lethal autonomous systems is a separate and serious question — but it is the only architecture that makes formal accountability possible at machine speed.
The Deeper Shift: Autonomous Systems That Build Themselves
The CRM was built by Claude Code in 17 minutes. Five parallel subagents, each with a single deliverable, governed by a formal topology that prevented them from contradicting each other. The KROG rules specified the build process, not just the output. The system was assembled correctly because the assembly process itself was formally governed.
This points toward something more significant than fast code generation.
When the specification is expressive enough to describe any permitted operation in any domain, and when the generation process is formally governed so that the generated system cannot violate the specification, then the human role in system development changes fundamentally.
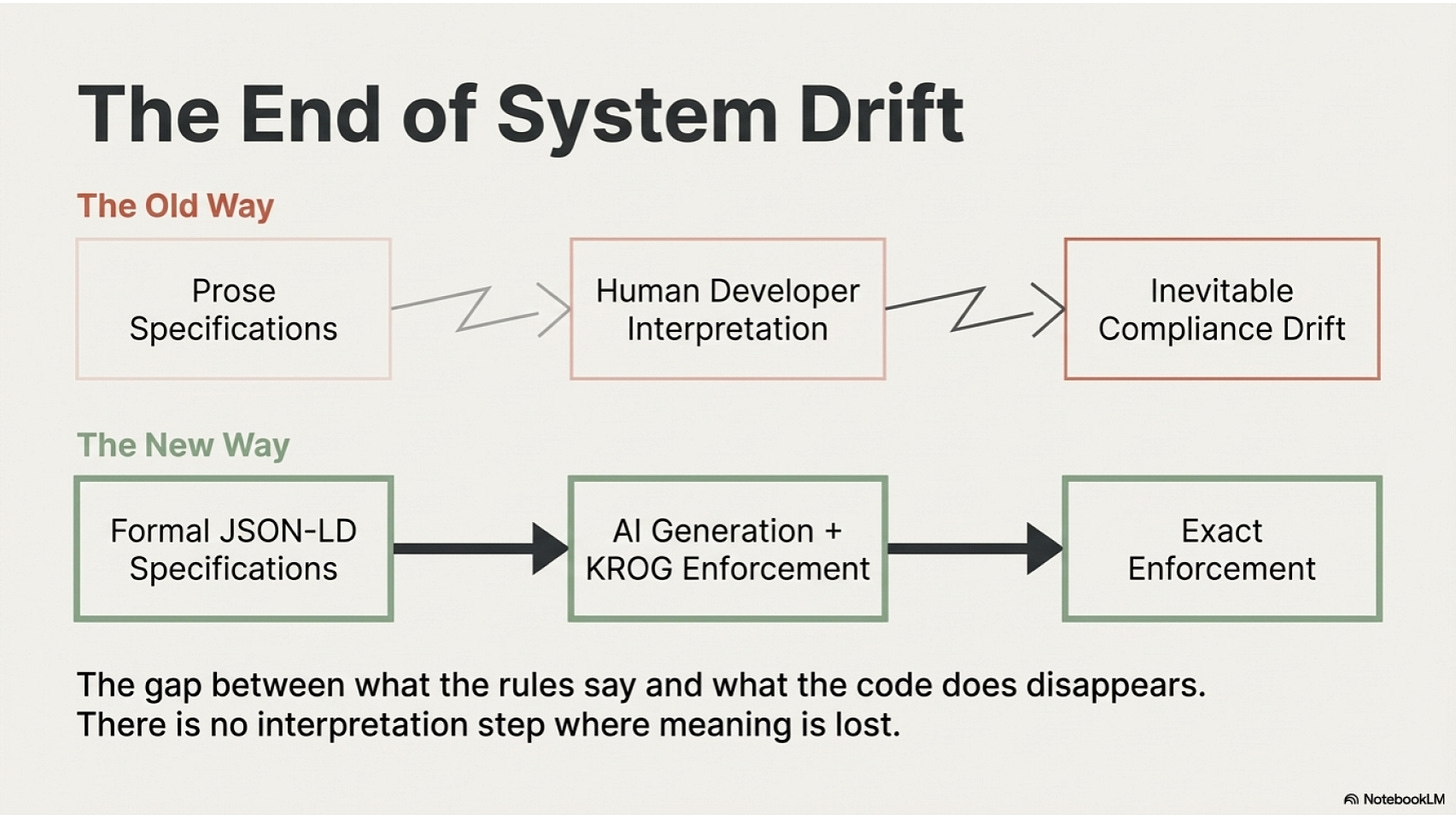
Today: humans write specifications (loosely, in prose), developers interpret them (imperfectly, in code), and the resulting system drifts from the original intent over time.
Tomorrow: humans write specifications (formally, in machine-readable structured data), AI agents generate systems that enforce them exactly, and the specification remains the authoritative source of truth throughout the system’s lifetime.
The drift problem — the gap between what the rules say and what the code does — disappears. Not because AI agents are infallible, but because the governance kernel that enforces the specification is compiled directly from the specification. There is no interpretation step where meaning is lost.
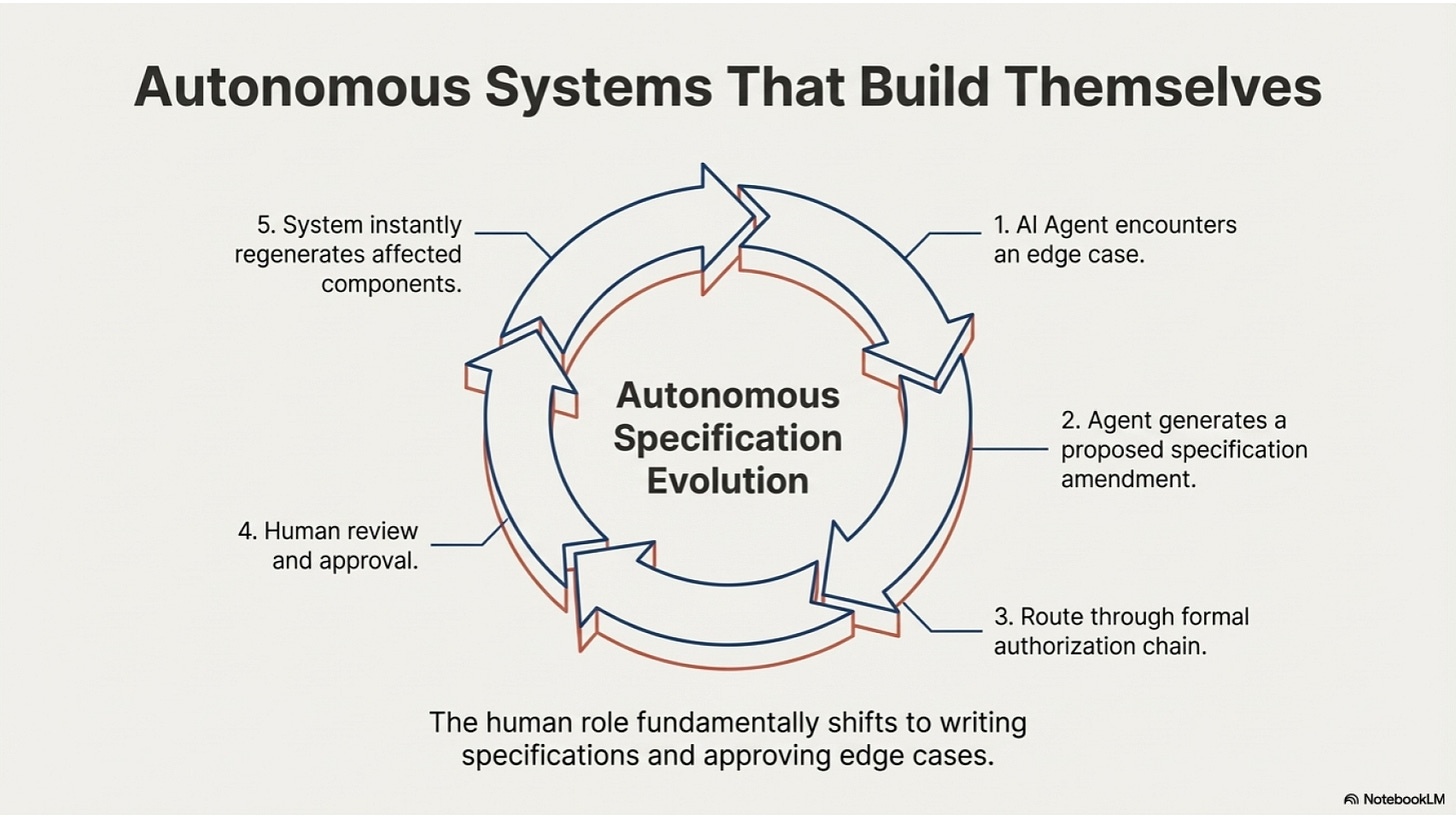
The next step beyond this is autonomous specification evolution. An AI agent operating under a specification, encountering a scenario the specification did not anticipate, generates a proposed specification amendment, routes it through the appropriate authorisation chain (which is itself specified), and upon approval, the system regenerates the affected components. The human role becomes: write the initial specification, approve amendments, review edge cases that exceed the agent’s authorisation to resolve.
This is not science fiction. The architecture is built. The KROG topology handles the authorisation chain. The governance kernel handles the enforcement. The audit trail handles the accountability. What remains is making the amendment proposal process smooth enough for human review at the pace AI agents generate edge cases.
The Missing Layer the EU Built the Plumbing For
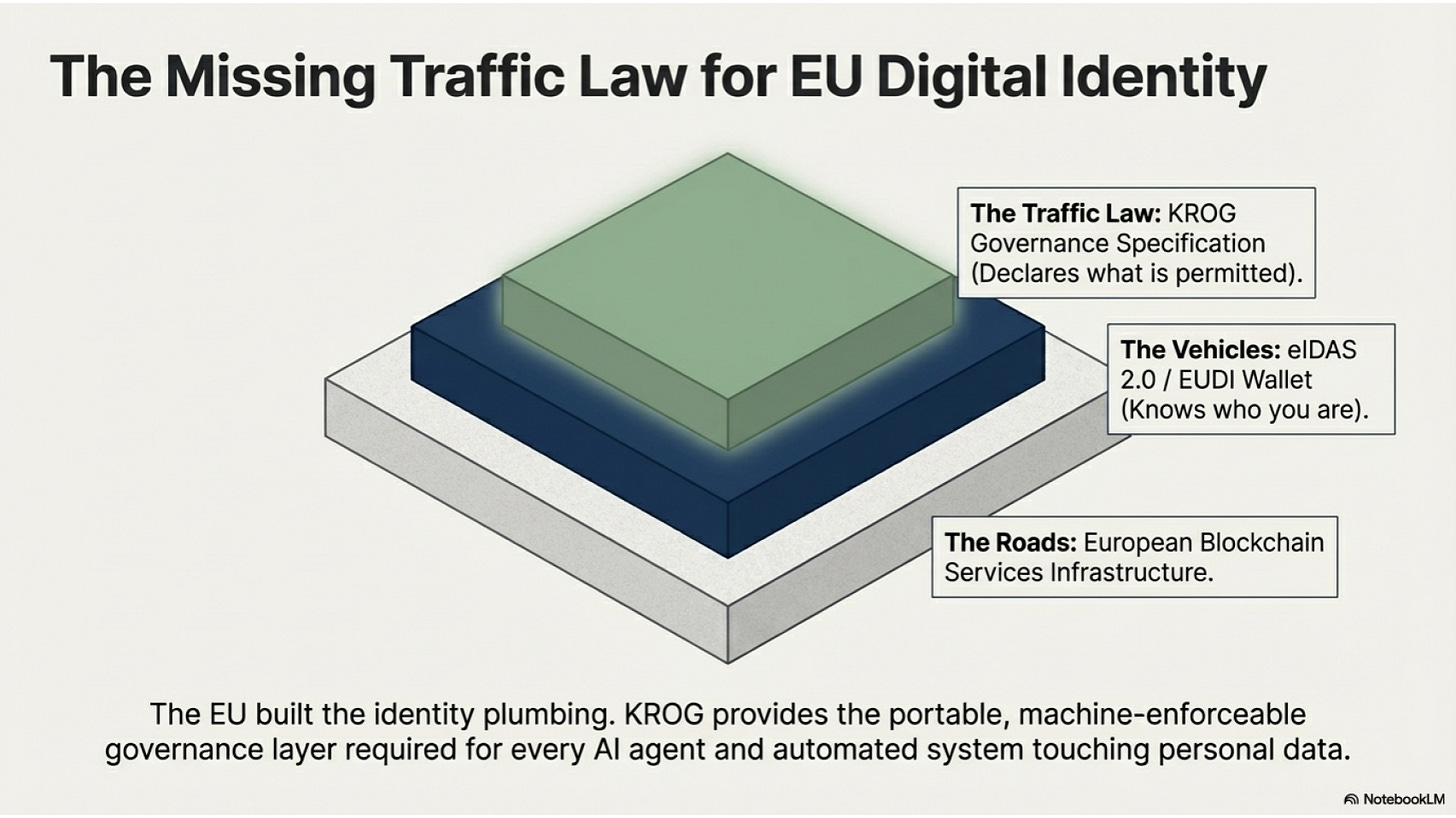
The European Union spent a decade building identity infrastructure. eIDAS 2.0, the European Digital Identity Wallet, the European Blockchain Services Infrastructure. The goal was portable, sovereign identity for individuals and organisations across member states.
What nobody built was the layer above it: the data governance specification that tells every system in the ecosystem what is permitted to happen to the data flowing through that identity infrastructure.
The EUDI Wallet knows who you are. It does not know what any given organisation is permitted to do with that knowledge. That permission layer — per data processing operation, machine-readable, formally governed, auditable — is the missing piece.
KROG is that layer.
The EU built the roads. eIDAS 2.0 built the vehicles. KROG is the traffic law — formally encoded, machine-enforceable, auditable by supervisory authorities, portable across jurisdictions.
Every AI agent, every automated system, every robot, every autonomous vehicle, every drone that touches (personal) data about a person with an EUDI Wallet credential will need to operate under a specification that declares what it is permitted to do. The specification will be issued by the data controller. The governance kernel will enforce it. The audit trail will be available to the supervisory authority.
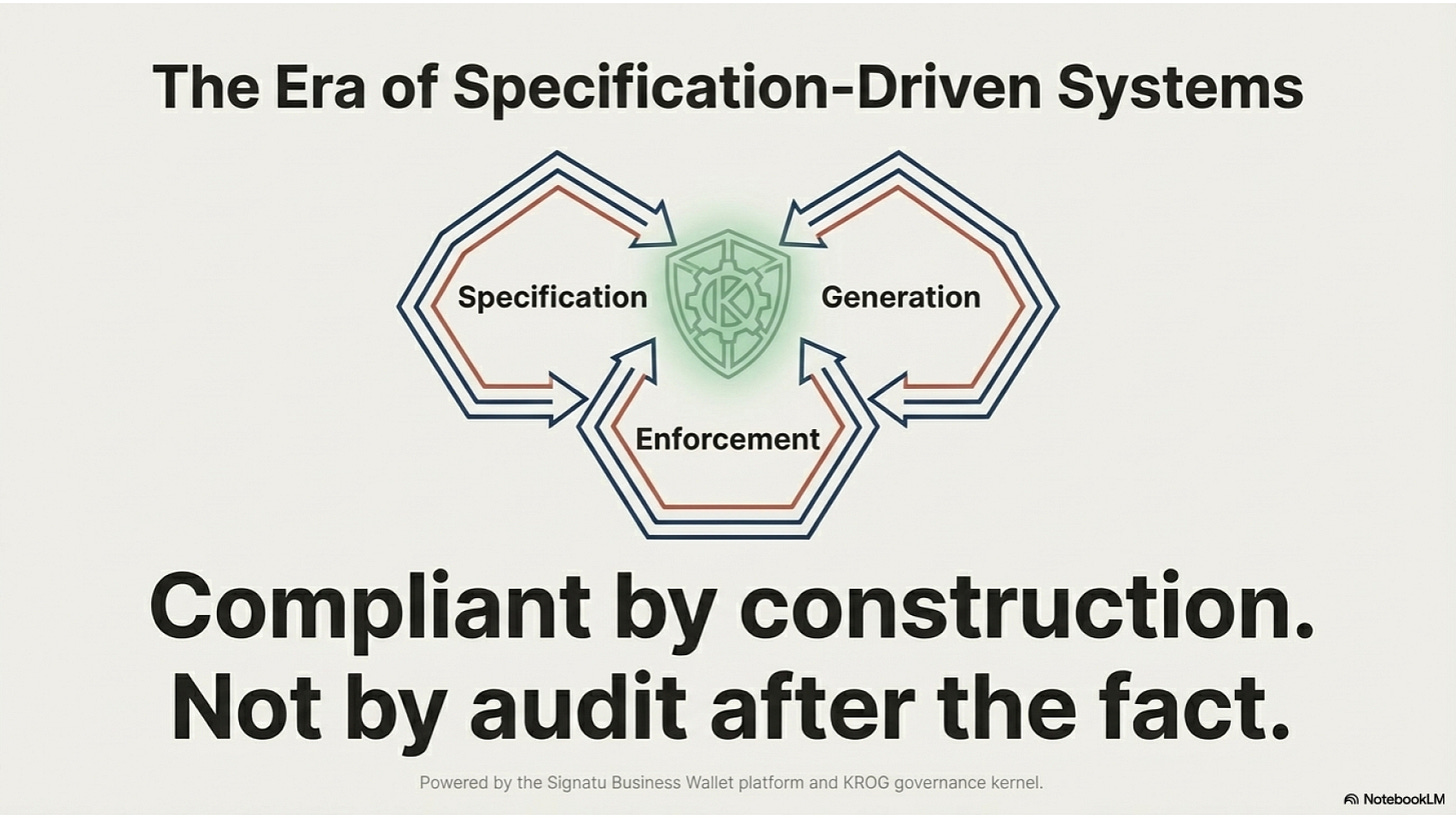
Compliant by construction. Not by audit after the fact.
What Seventeen Minutes Means
A system that would have taken three months to specify, architect, build, test, and certify was generated in seventeen minutes because the specification was already formal and the generation process was formally governed.
This is not an efficiency gain. It is a category change.
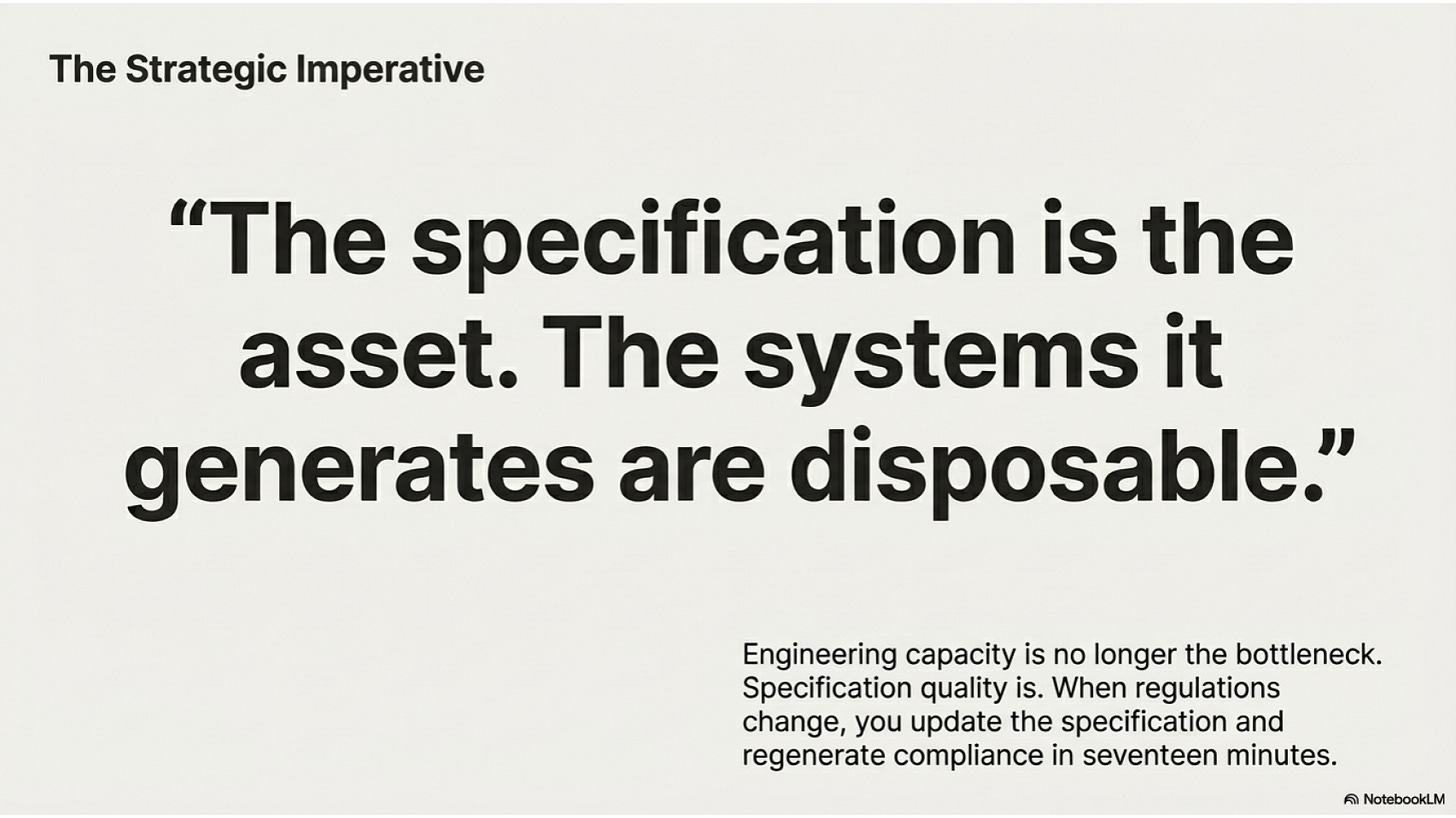
When the cost of generating a governed system approaches zero, the constraint on deploying governed systems is no longer engineering capacity. It is specification quality. The bottleneck moves from can we build it to can we specify it precisely enough.
Every organisation that invests in writing precise, machine-readable specifications for its data operations — not for compliance documentation, but as the actual governing instrument from which its systems are generated — will have a structural advantage over organisations that continue to build systems first and document compliance after.
The specification is the asset. The systems it generates are disposable. When the regulatory environment changes, you update the specification, regenerate the affected components, and the system is compliant again — in seventeen minutes.
The CRM described in this post was generated from a JSON-LD specification using the KROG Business Wallet platform and KROG governance kernel. The full specification, prompt, and verification results are documented in the build log.
KROG builds the data governance layer for the era of AI agents — specification-driven, KROG-governed, compliant by construction.