KROG Wallets — Consultation Response for European Business Wallets
The Future in Your Pocket: 5 Surprising Ways the EU Digital Identity Wallet is Changing Forever
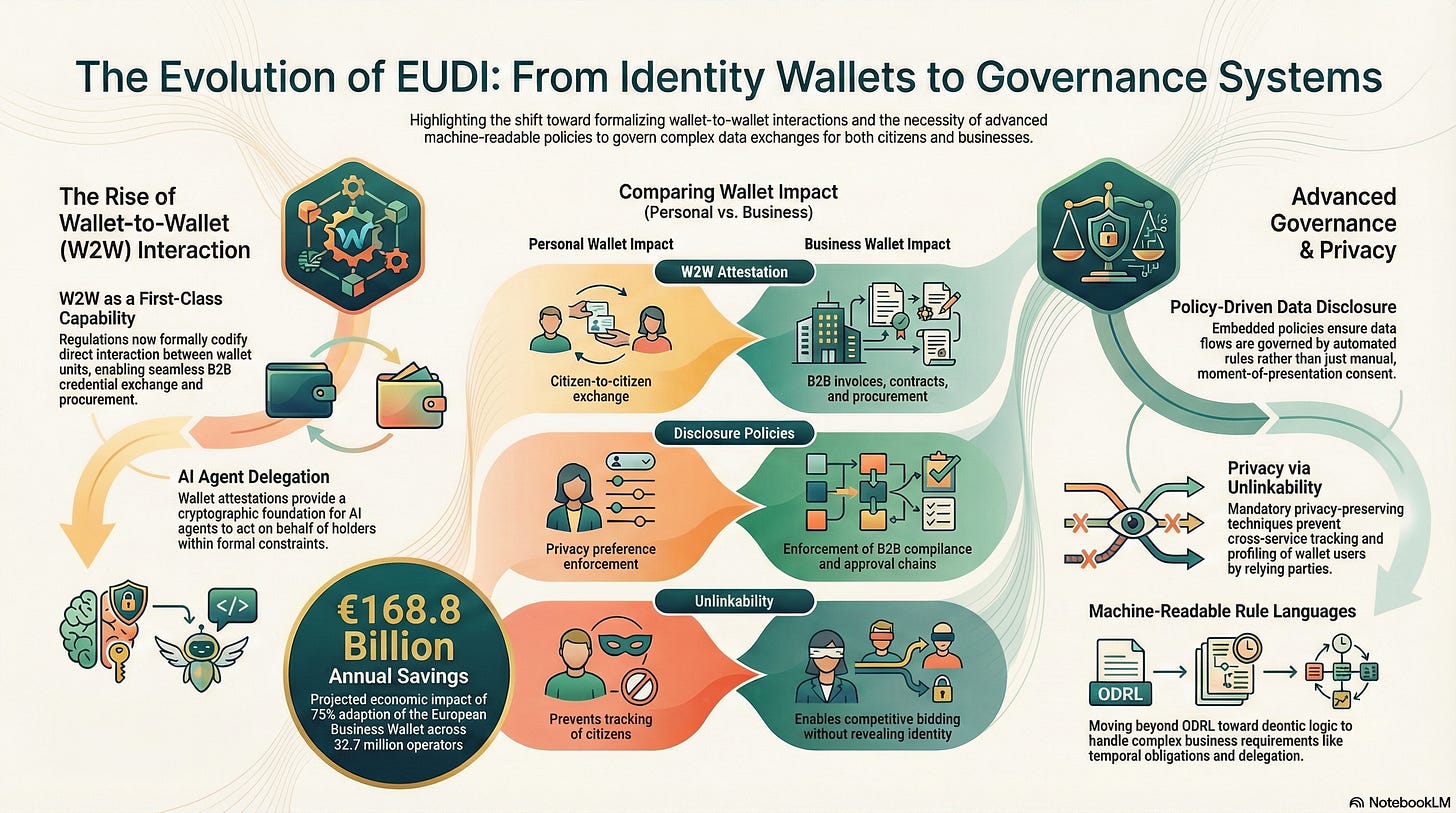
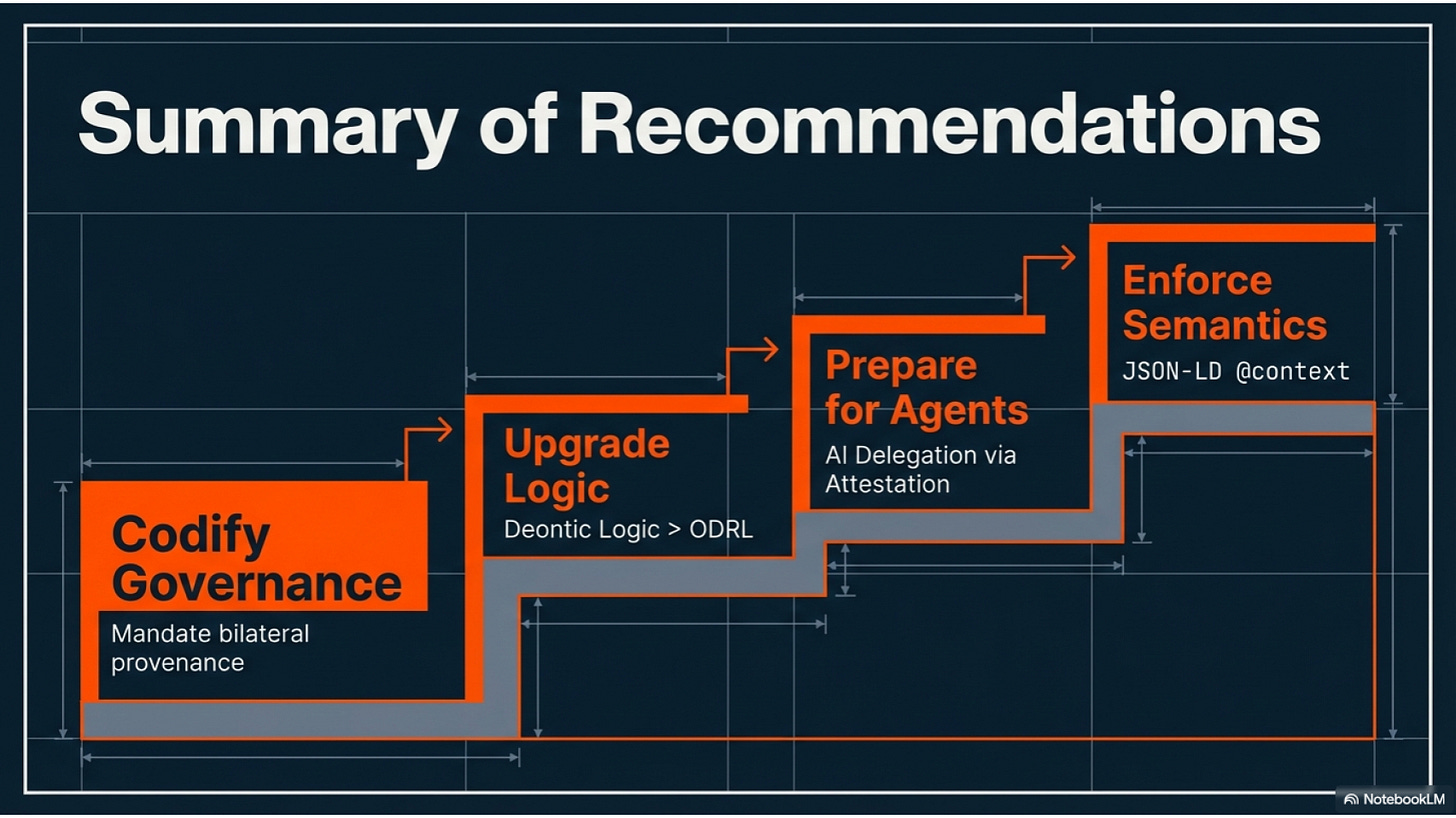
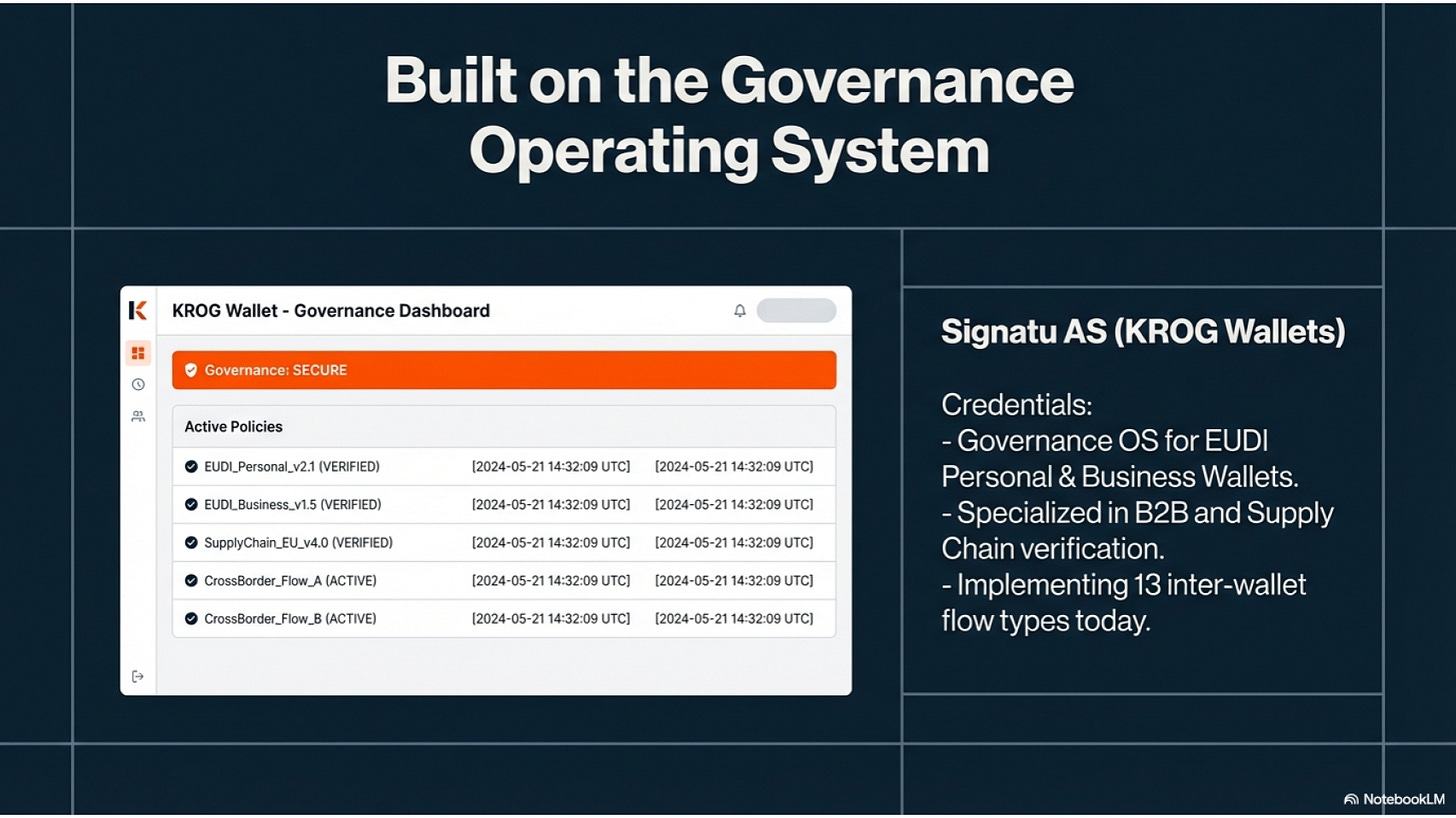
This week, I handed in our formal consultation response regarding proposed updates to the European Digital Identity (EUDI) Wallet regulations. We express strong support for new technical standards governing wallet-to-wallet communication and embedded disclosure policies. These amendments are viewed as essential for enabling secure business-to-business exchanges, automated procurement, and the delegation of tasks to AI agents. We suggest incorporating more advanced machine-readable policy languages to handle complex legal and contractual obligations. We emphasize that these personal wallet standards must remain compatible with the forthcoming European Business Wallet framework to ensure seamless economic integration. Below is a tiny and easy to digest version of our ideas.
1. Introduction: The Evolution of the Digital Handshake
For years, the European Digital Identity (EUDI) Wallet was dismissed by many as a glorified digital folder—a secure app to hold a driver’s license or a travel permit. But as the technical “plumbing” of the ecosystem matures, that old view is being demolished. We are moving away from a world of simple visual inspection toward a future defined by algorithmic negotiation.
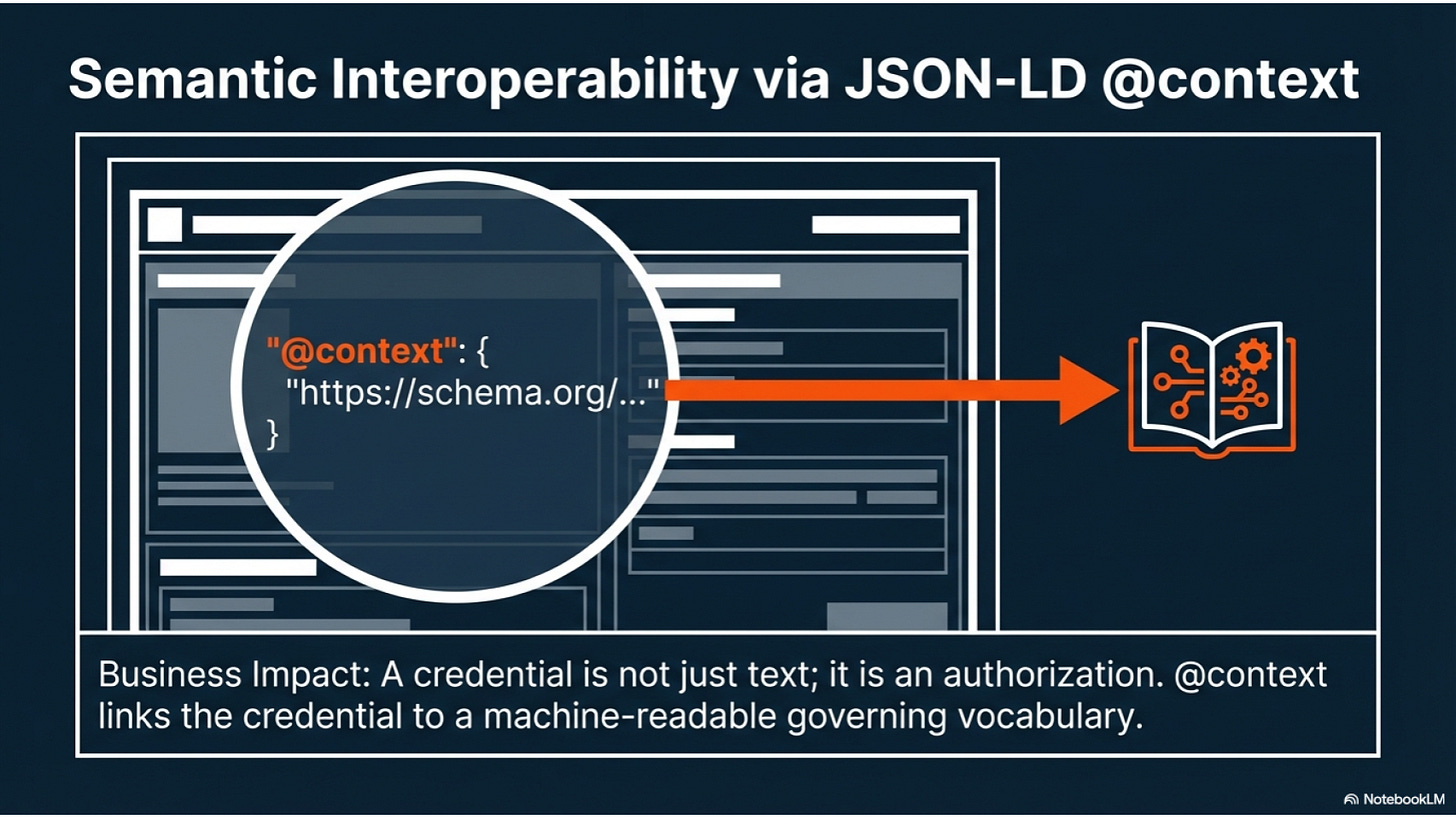
The EUDI Wallet is no longer just a tool for “carrying your ID”; it is evolving into a sophisticated governance operating system. This shift represents a fundamental change in our digital agency. Your wallet is transitioning from a passive container into an active orchestrator, capable of shielding your privacy, enforcing your legal rights, and even acting on your behalf. As we peel back the layers of recent regulatory updates, we see a roadmap for a device that manages your commercial and legal presence in a microsecond.
2. Takeaway 1: Your Wallet is Learning to Talk to Other Wallets
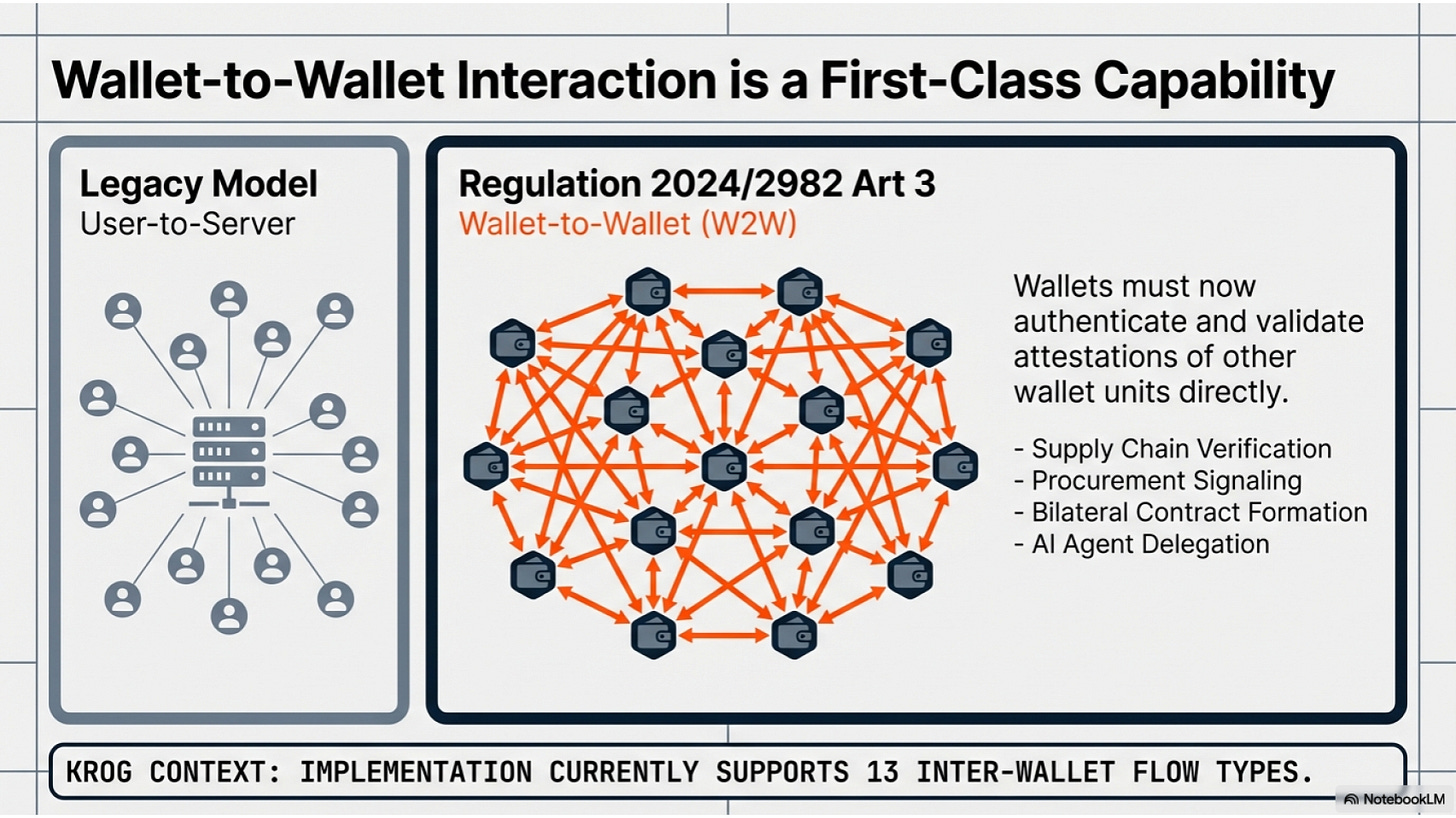
In the early days of digital identity, the focus was almost entirely on “wallet-to-relying-party” flows—presenting a credential to a bank or a government portal. However, recent amendments (such as those to Regulation 2024/2982) have formally codified wallet-to-wallet (W2W) interaction as a “first-class capability.”
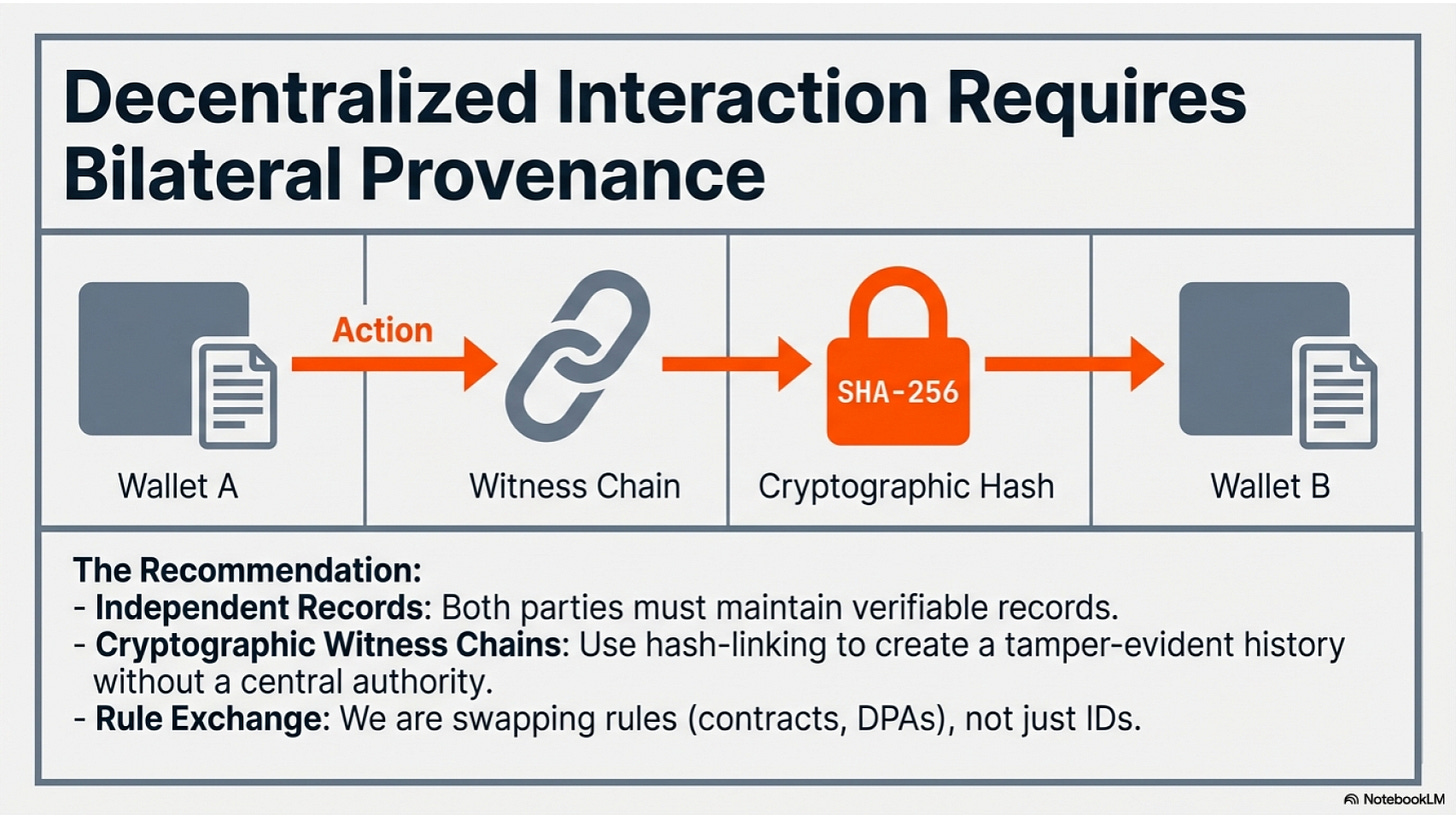
This shift enables what experts call bilateral provenance. In this model, two private parties can interact without a central authority acting as an intermediary. To ensure this remains secure and verifiable, the system utilizes “cryptographic witness chains” to create a private, immutable audit trail of the interaction.
“Bilateral provenance: When two wallet units interact, both parties should maintain independent, verifiable records of the interaction. Our implementation uses cryptographic witness chains where both wallets record the action, the rule that authorized it, and a hash linking it to the previous event.”
This isn’t just a technical nuance; it is the infrastructure for peer-to-peer commerce and bilateral contract formation. It allows two individuals or businesses to exchange enforceable rules—like a Data Processing Agreement—directly from pocket to pocket.
3. Takeaway 2: The Rise of the AI Agent Proxy
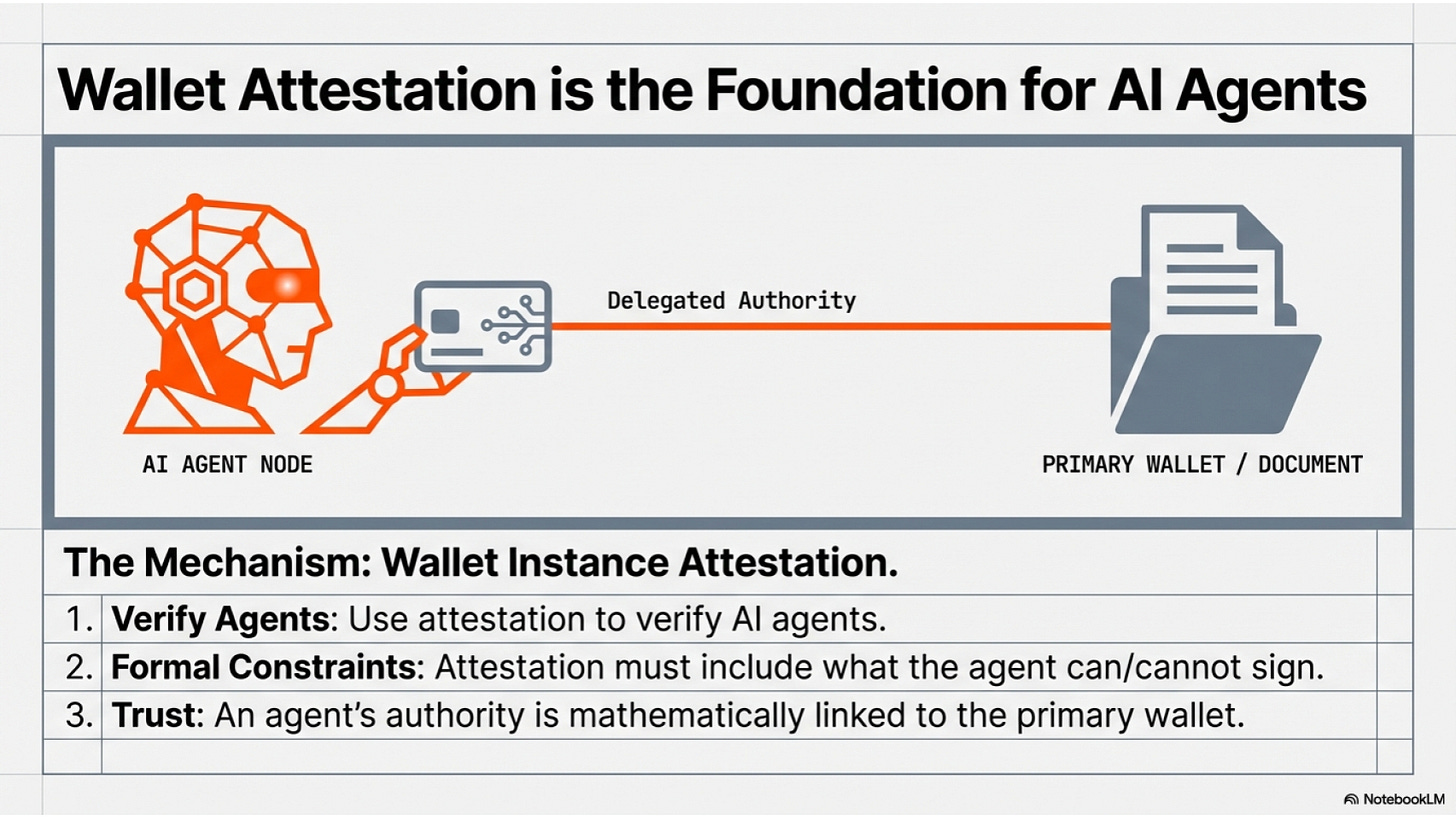
The Mechanics of Delegation Perhaps the most visionary aspect of the new framework is the formalization of “AI agent delegation.” The system now anticipates a future where you don’t perform every digital interaction yourself. Instead, you can “deputize” an AI agent to handle specific tasks. Crucially, this is secured via the wallet instance attestation mechanism. This is the same high-level security that proves your wallet is legitimate and uncompromised, and it is now being used to attest that your AI agent has the formal authority to act on your behalf.
Acting Within Formal Constraints The power of this delegation lies in its precision. You aren’t giving an AI agent a blank check; you are authorizing it to act within “formal constraints.” Whether it’s negotiating a service agreement or managing complex data consents, the agent’s authority is cryptographically bound. This allows for seamless automation of our digital lives without sacrificing the security of the underlying identity.
4. Takeaway 3: The €168 Billion “Business Wallet” Opportunity
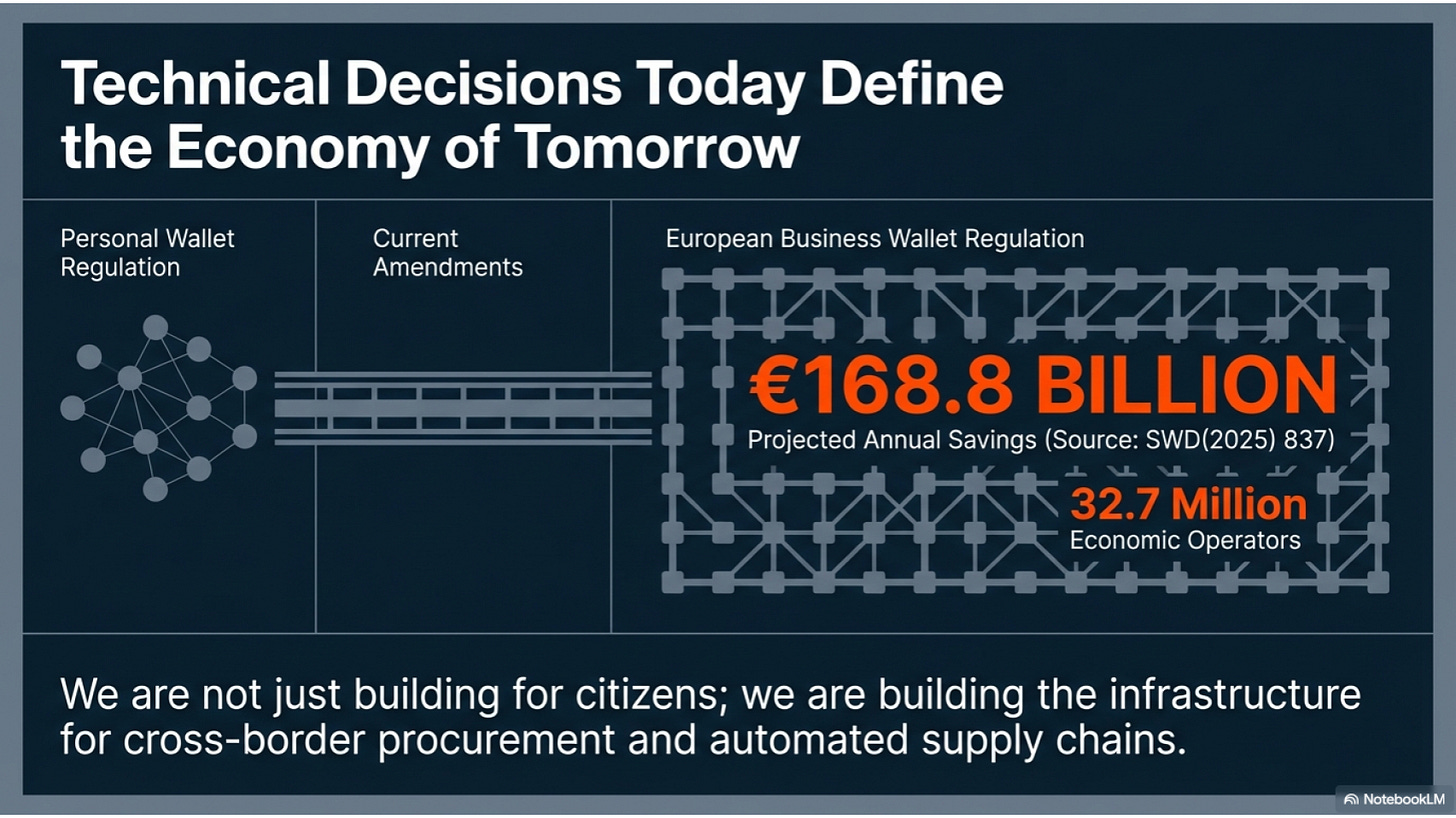
While the personal wallet gets the headlines, the most significant economic shift may come from the European Business Wallet (EUBW). With the European Commission projecting €168.8 billion in annual savings at a 75% adoption rate across 32.7 million economic operators, the stakes are staggering.
The “strategic edge” for businesses lies in privacy-preserving unlinkability. In a high-stakes procurement scenario, a company can signal its interest in a multi-million euro contract—proving it has the necessary capital and credentials—without revealing its identity to competitors or the market at large. This “procurement signaling” ensures that businesses can engage in competitive bidding while keeping their market strategy shielded until the final stages of a transaction.
5. Takeaway 4: Governance That Happens Before You Hit “Accept”
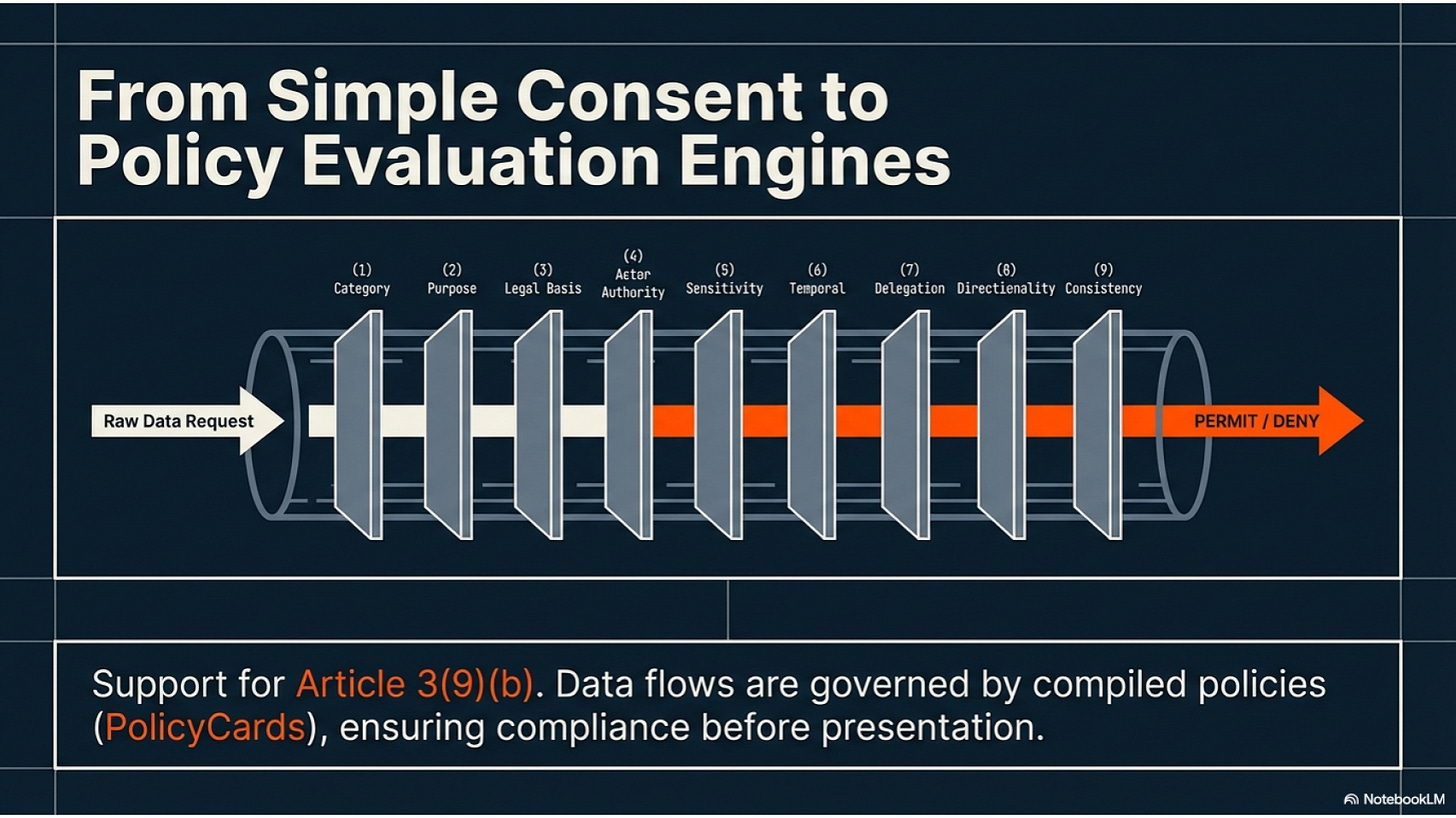
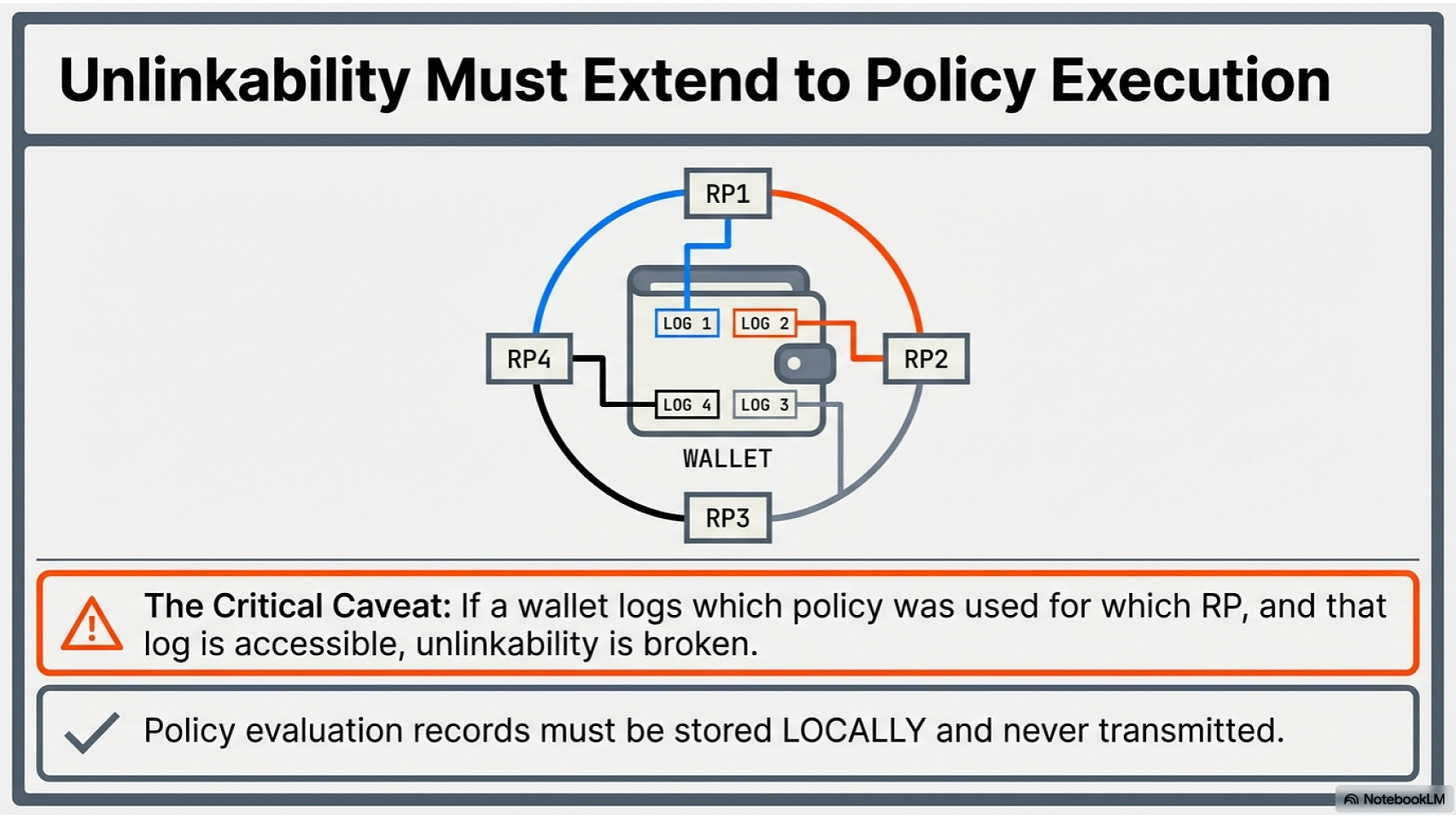
The era of blindly clicking “I Accept” on a 50-page terms-of-service document is coming to an end. Under Article 3(9)(b), the EUDI ecosystem is introducing Embedded Disclosure Policies. This moves the responsibility of protection from the user to a “Gateway evaluation engine” within the wallet.
Before any data is released, the wallet processes a set of PolicyCards—compiled disclosure rules—against a rigorous 9-step criteria. This engine evaluates factors such as:
Legal basis: Does the requester have a valid reason to ask?
Actor authority level: Is this entity authorized to handle this specific data?
Temporal constraints: Is the request happening within a permitted timeframe?
Data flow directionality: Where is this data actually going?
Purpose limitation: Is the data being used for the stated goal?
This ensures that the wallet acts as a proactive guardian, doing the heavy lifting of data protection before a human even sees a notification.
“The governance layer—the rules that determine what happens to data before, during, and after wallet interactions—is as important as the identity layer.” (Conclusion, KROG Consultation Response)
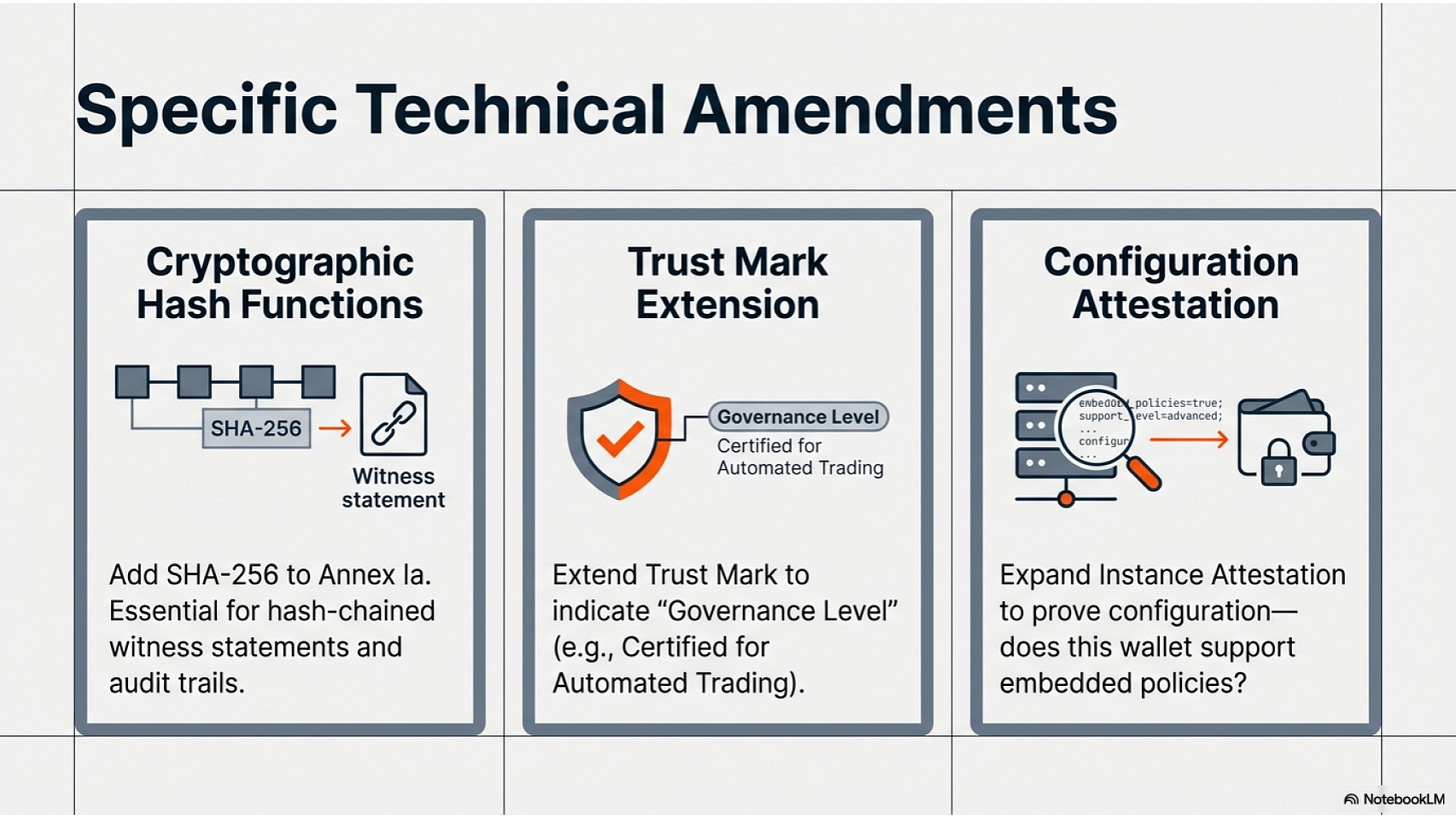
6. Takeaway 5: Beyond Simple Permissions (The ODRL Limitation)
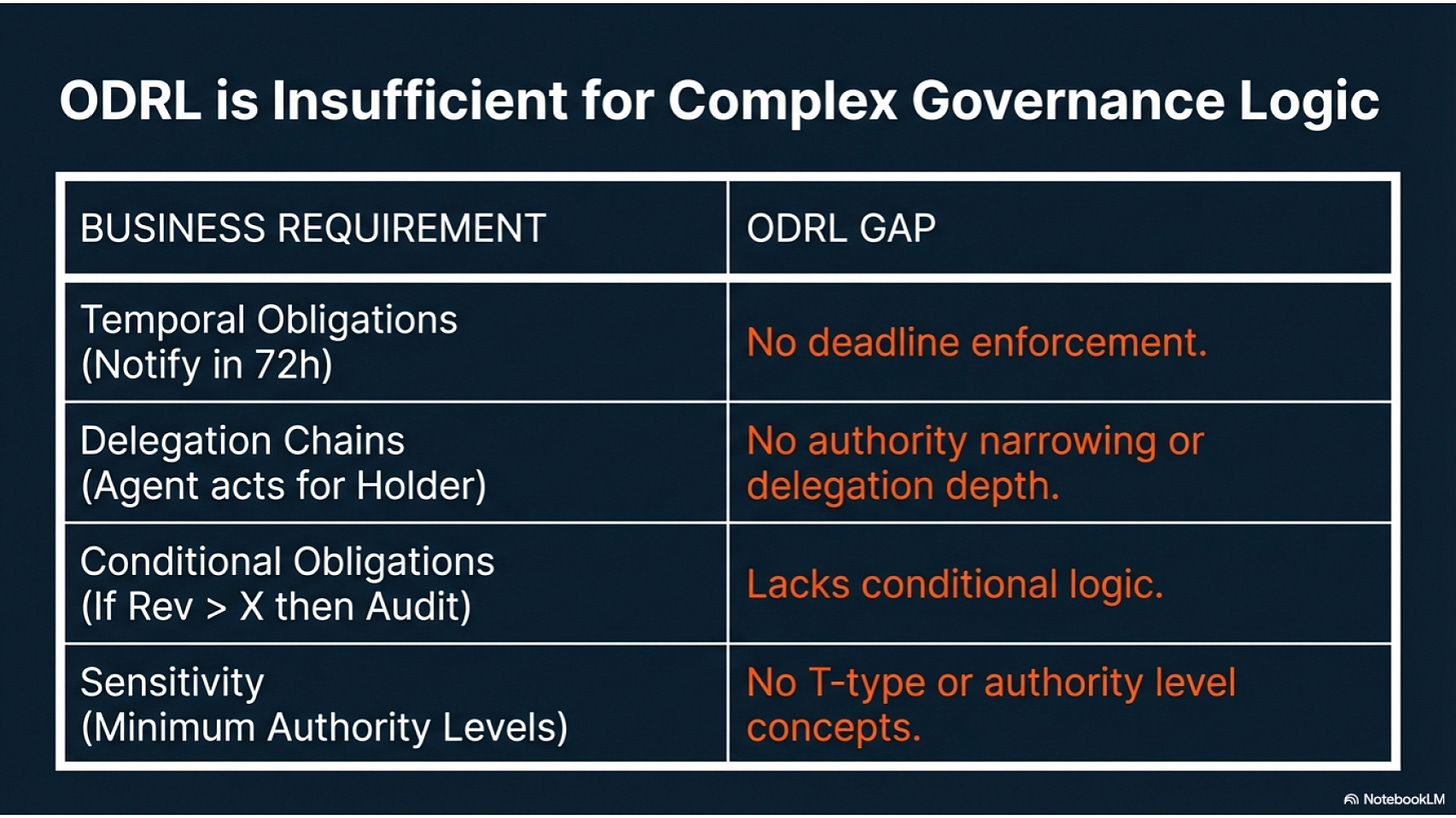
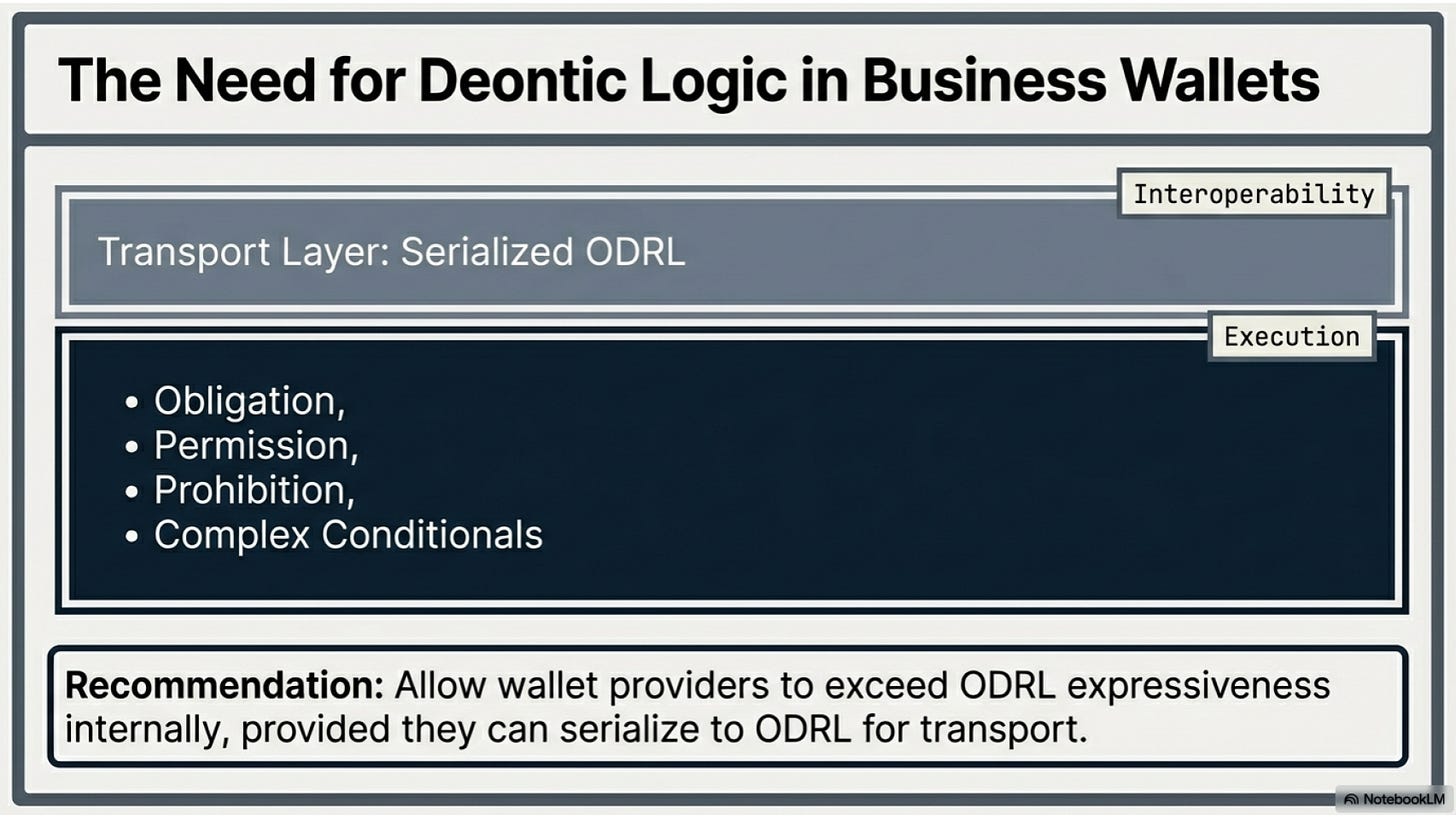
Most current digital rights systems use ODRL (Open Digital Rights Language), which relies on simple “permit” or “prohibit” logic. However, real-world business is defined by bilateral asymmetry—where different parties have different risks and obligations.
To handle the complexity of modern commerce, the EUDI framework is moving toward rule logic. For example, it can enforce a “temporal obligation,” such as a rule requiring a specific notification to be sent “within 72 hours” of a contract event. By moving to this richer logic, the wallet becomes capable of managing multi-party contracts and automated business compliance that simple “yes/no” permissions simply cannot handle.
7. Conclusion: From “Who You Are” to “What You Can Do”
The ultimate success of the EUDI Wallet will not be measured by how well it proves your identity, but by how well it proves your authorizations. We are witnessing a shift from a world of “Who are you?” to a world of “What are you authorized to do?”
As these technical specifications become reality, the wallet is transforming into a verifiable decision-maker, shifting the power dynamic of the digital world back to the individual and the business. This leads to a provocative new reality: are you ready to trust an algorithm to defend your legal rights in a microsecond negotiation?